Understanding 'Access Denied' so that permissions can be reverted - icacls and takeown
How to view permissions of Accessed Denied Folder in Windows 10
I guessed that system would be one user that would have access to this folder, so following after that thought I found a solution for running command prompt as system.
See - SO How do you run CMD.exe under the Local System Account?
- Download PStools from SysInternals, Microsoft.
- Run CMD as admin, navigate to folder of psexec.exe & psexec64.exe and run the following:
psexec -i -s cmd.exe
or if you want 64 bit...
psexec64 -i -s cmd.exe
Now a command prompt window has opened as system.
Now we can view the permissions of the folder...
icacls C:\ProgramData\Microsoft\Windows\SystemData
C:\ProgramData\Microsoft\Windows\SystemData
NT SERVICE\TrustedInstaller:(F)
NT AUTHORITY\SYSTEM:(F)
- Also an ACL can now be saved and resoted as described here
icacls C:\ProgramData\Microsoft\Windows\SystemData /save "C:\SystemData.acl" /t
icacls C:\ProgramData\Microsoft\Windows /restore "C:\SystemData.acl"
- In standard admin Command Prompt, not system, have yet to workout how to restore ownership like this after using takeown. Currently using the above System Command Prompt or ACL solution permissions can be restored. However have discovered that one can just run a batch script through task scheduler as System, then one does not need to change permissions.
Reading:
- SO - How do you run CMD.exe under the Local System Account? Solution 1
- SO - How do you run CMD.exe under the Local System Account? Solution 2
- Understanding how to use Icals & Takeown to make changes and reset in Windows 10
Related videos on Youtube
Giacomo1968
Updated on September 18, 2022Comments
-
 Giacomo1968 over 1 year
Giacomo1968 over 1 year- Before taking ownership of files and folders I would like to understand how to view the current permissions so that they may be reverted.
- I am reciving an 'Access Denied' message to view or save permissions with elevated command prompt for location: C:\ProgramData\Microsoft\Windows\SystemData in Windows 10 enviroment.
- It looks like that I may need to take ownership first, then can view the permissions, and use something like icacls 'reset' command to fix it afterwards.
If I try to view permissions:
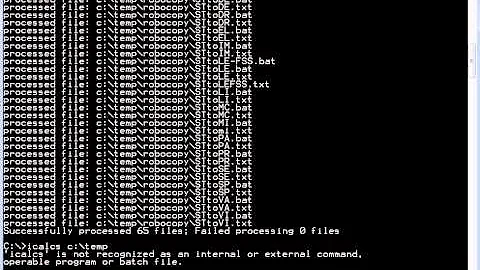
C:\Windows\system32>icacls "C:\ProgramData\Microsoft\Windows\SystemData" C:\ProgramData\Microsoft\Windows\SystemData: Access is denied. Successfully processed 0 files; Failed processing 1 filesIf I try to save an ACL file:
C:\Windows\system32>icacls C:\ProgramData\Microsoft\Windows\SystemData /save "C:\SystemData.acl" /t C:\ProgramData\Microsoft\Windows\SystemData: Access is denied. Successfully processed 0 files; Failed processing 1 filesIn the answer to 'Understanding how to use Icals & Takeown' the owner of the folder was NT SERVICE\TrustedInstaller which may infact may be a standard in Windows 10, though I am only guessing.
Should I just use takeown, and icals, find out the permissions and then use the reset command.
takeown /f C:\ProgramData\Microsoft\Windows\SystemData /r icacls C:\ProgramData\Microsoft\Windows\SystemData /grant "%USERDOMAIN%\%USERNAME%":(F) /t Make Changes icacls C:\ProgramData\Microsoft\Windows\SystemData /setowner "NT SERVICE\TrustedInstaller" /t icacls C:\ProgramData\Microsoft\Windows\SystemData /reset /tLikewise with the ACL, one would need to take ownership before creating, or is there a work around?
Reading:
- SU - Understanding how to use Icals & Takeown to make changes and reset in Windows 10
- SU - Create List of Access Denied Files & Folders
- SU - Setting Deny Permissions with ICACLS on “This Folder”
- SU - Is there a way in which I can use takeown to apply ownership to every directory on the drive?
- SU - Takeown grant permission
- SU Can I revert changes from the TAKEOWN and ICACLS commands?
- Howtogeek - Reverse take ownership
- Faqforge - Take Ownership of a File or Folder by Command in Windows
- Microsoft - ICACLS setowner and GRANT operation appears to be causing some existing perms on subfolders to be removed. Why
- Itprotoday - Removing a User or Group’s Permissions
- SS46 - Takeown
- SS64 - Icacls