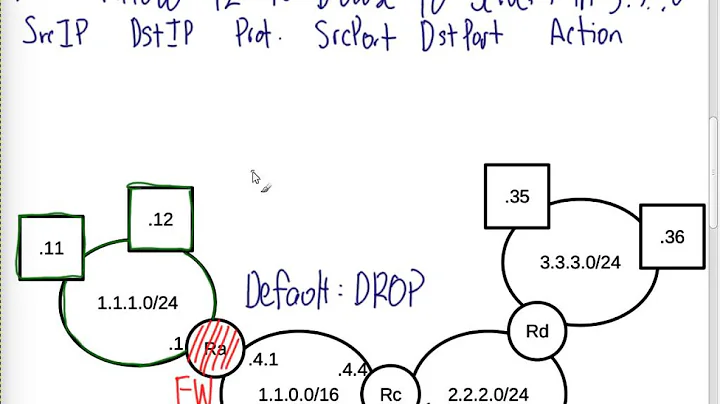
What is the default action for incoming packets that don't match explicit iptables rules?
Solution 1
It depends on your policy, you can set to reject or accept if incoming packets don't explicity match rules (I think by default it will DROP). You can set default policy by using -P option:
# accept by default
iptables -P INPUT ACCEPT
# drop by dèault
iptables -P INPUT DROP
Solution 2
(iptables -L INPUT; iptables -L OUTPUT; iptables -L FORWARD) | grep policy
Chain INPUT (policy DROP)
Chain OUTPUT (policy ACCEPT)
Chain FORWARD (policy DROP)
iptables -P sets the policy for a chain.
man iptables:
Only built-in (non-user-defined) chains can have policies, and neither built-in nor user-defined chains can be policy targets.
The big difference from a structure perspective is: If a user defined chain reaches its end without an explicit decision then the control flow goes back to the calling chain from whose perspective the jump to the called chain was just like any other rule which either matches or doesn't.
Related videos on Youtube
Mike B
Updated on September 18, 2022Comments
-
 Mike B over 1 year
Mike B over 1 yearCentOS 5.x
I'd like to understand what is specifically happening to incoming packets that don't explicitly match rules in my iptables chains. Is the default action to reject them? Or drop them? How/where can I set this?
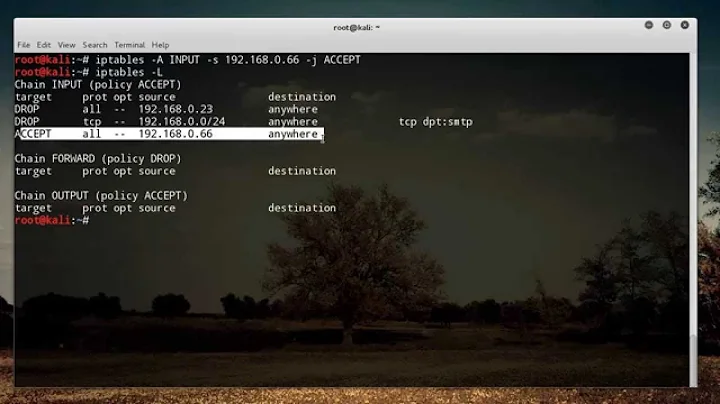
Here's an example output of my firewall setup (some ports have been modified to protect the innocent :-) ) :
Chain INPUT (policy ACCEPT) target prot opt source destination RH-Firewall-1-INPUT all -- anywhere anywhere Chain FORWARD (policy ACCEPT) target prot opt source destination RH-Firewall-1-INPUT all -- anywhere anywhere Chain OUTPUT (policy ACCEPT) target prot opt source destination Chain RH-Firewall-1-INPUT (2 references) target prot opt source destination ACCEPT all -- anywhere anywhere ACCEPT all -- anywhere anywhere ACCEPT icmp -- anywhere anywhere icmp any ACCEPT esp -- anywhere anywhere ACCEPT ah -- anywhere anywhere ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:456 REJECT all -- anywhere anywhere reject-with icmp-host-prohibitedThe key point though is that I have a different chain called
RH-Firewall-1-INPUTthat doesn't have an explicit(policy ACCEPT)or(policy REJECT)statement. What would be the default behavior for that (assuming of course that I'm NOT matching any of the prior rules). Is the last line just a "catch all"? -
 Mike B about 10 yearsI have another chain that doesn't explicitly have a single policy action in parenthesis. I've updated the question description. Can you please review?
Mike B about 10 yearsI have another chain that doesn't explicitly have a single policy action in parenthesis. I've updated the question description. Can you please review?
![IPTABLES [PART-1] : "UNDERSTANDING THE CONCEPT"](https://i.ytimg.com/vi/vbhr4csDeI4/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBovKYd5heeT0eQFP4enqBJ_GCa1Q)