Which TLS protocols are enabled in Ubuntu 14.04's OpenSSL?
47,594
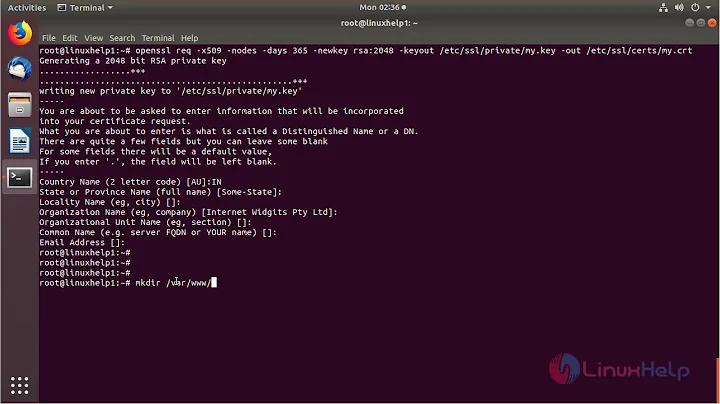
Solution 1
$ cat /etc/issue
Ubuntu 14.04 LTS \n \l
$ apt-cache policy openssl
openssl:
Installed: 1.0.1f-1ubuntu2
Candidate: 1.0.1f-1ubuntu2
Version table:
*** 1.0.1f-1ubuntu2 0
500 http://us.archive.ubuntu.com/ubuntu/ trusty/main amd64 Packages
100 /var/lib/dpkg/status
$ openssl ciphers -v 'TLSv1.2' | head -4
ECDHE-RSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AESGCM(256) Mac=AEAD
ECDHE-ECDSA-AES256-GCM-SHA384 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AESGCM(256) Mac=AEAD
ECDHE-RSA-AES256-SHA384 TLSv1.2 Kx=ECDH Au=RSA Enc=AES(256) Mac=SHA384
ECDHE-ECDSA-AES256-SHA384 TLSv1.2 Kx=ECDH Au=ECDSA Enc=AES(256) Mac=SHA384
Solution 2
I would like to summarize the answer by @andrewsomething...
Short answer TLSv1.2.
Specifically on your system use the command:
$ openssl ciphers -v TLSv1
You can replace v1 with v1.[012] as needed to see details. Note you will want to use TLSv1 and TLSv1.2 (1.0 and 1.1 are disabled by default).
Solution 3
openssl ciphers -v | awk '{print $2}' | sort | uniq
Should print what is enabled.
Related videos on Youtube
Author by
Community
Updated on September 18, 2022Comments
-
Community over 1 year
This is a follow up to Override Distro Package with Custom Package?.
Does anyone know if Ubuntu 14.04's OpenSSL enables all TLS protocols (TLS1.0, TLS1.1 and TLS1.2)? Or does it have protocols disabled (TLS1.1 and TLS1.2) like past versions?
Related: how does one even check for this sort of thing?
Edit: This is not a bug report question; nor is it a developer question. You guys are taking the "Close as Bug Report" much too far.
-
 Admin about 10 yearsIMO it depends on the specific client (browser, email, etc.), not the OS.
Admin about 10 yearsIMO it depends on the specific client (browser, email, etc.), not the OS. -
 Admin about 10 yearsThanks Braiam. Ubuntu will disable them. The clients and server have no choice. See, for example, OpenSSL downlevel version is 1.0.0, and does not support TLS 1.2.
Admin about 10 yearsThanks Braiam. Ubuntu will disable them. The clients and server have no choice. See, for example, OpenSSL downlevel version is 1.0.0, and does not support TLS 1.2. -
 Admin about 10 yearsI think upstream fixed the problems, I wasn't able to reproduce the issue in Debian Testing, which uses OpenSSL 1.0.1f, so I think that Ubuntu will just import that. If you want to verify just download a copy of Ubuntu 14.04 and test it.
Admin about 10 yearsI think upstream fixed the problems, I wasn't able to reproduce the issue in Debian Testing, which uses OpenSSL 1.0.1f, so I think that Ubuntu will just import that. If you want to verify just download a copy of Ubuntu 14.04 and test it. -
 Admin about 10 yearsThanks Braiam. So I'm clear, what cipher is negotiated with this command:
Admin about 10 yearsThanks Braiam. So I'm clear, what cipher is negotiated with this command:openssl s_client -connect mail.google.com:443 -servername mail.google.com -tls1_2 -no_comp? It should be one of theECDHE-ECDSAciphers likeECDHE-ECDSA-AES128-GCM-SHA256. -
 Admin about 10 yearsfor me
Admin about 10 yearsfor meNew, TLSv1/SSLv3, Cipher is ECDHE-ECDSA-AES128-GCM-SHA256in Debian. -
 Admin about 10 yearsPerfect, thank you very much. The
Admin about 10 yearsPerfect, thank you very much. TheECDHE-ECDSAciphers are only available in TLS 1.2 (and above, whenever that comes). -
 Admin about 10 yearsJust to clarify, the reason this is closed is because 14.04 hasn't been released yet, although I think since all the freezes have happened and you have an answer we can reopen it. @Braiam Please post an answer if you can.
Admin about 10 yearsJust to clarify, the reason this is closed is because 14.04 hasn't been released yet, although I think since all the freezes have happened and you have an answer we can reopen it. @Braiam Please post an answer if you can. -
 Admin about 10 years@Seth no, the reason is because it's a bug. Trusty doesn't have imported the patch. OP needs to ask for a Feature Freeze exception as described in the wiki page wiki.ubuntu.com/… if he wants the bug fixed for Trusty before final release.
Admin about 10 years@Seth no, the reason is because it's a bug. Trusty doesn't have imported the patch. OP needs to ask for a Feature Freeze exception as described in the wiki page wiki.ubuntu.com/… if he wants the bug fixed for Trusty before final release. -
 Admin about 10 years@Braiam No, the OP asked if it had the feature. Nothing to do with a bug.
Admin about 10 years@Braiam No, the OP asked if it had the feature. Nothing to do with a bug.
-