Why does SNAT happen in POSTROUTING chain and DNAT in PREROUTING chain?
Solution 1
Usually the main criterion for SNAT is "traffic that's going out a given interface" (i.e. -o eth0). What interface a packet will go out is determined by routing, so to apply that criterion you need to run it in a POSTROUTING context.
DNAT rewrites the destination address of a packet, meaning it can affect where a packet goes to — for example, a packet that looks like it's destined for the gateway could end up being rewritten to go to a machine on the network instead. Since you want the routing to be able to take that rewritten destination into account when it makes its decision, so that the packet actually goes where it needs to, DNAT should run in a PREROUTING context.
Solution 2
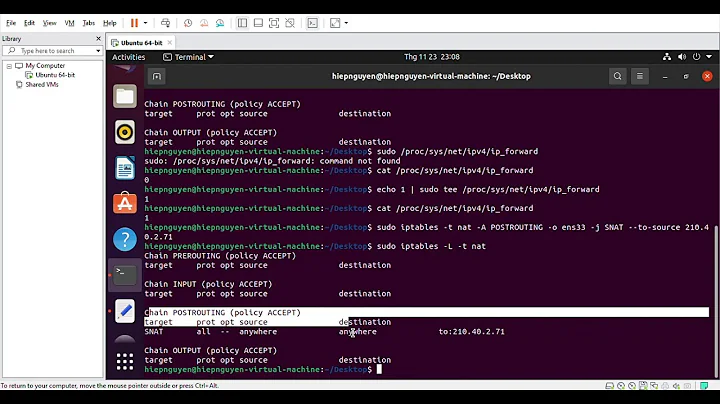
I'm pretty sure anything coming from the local machine never goes through the PREROUTING table, as seen in this awesome ASCII figure.
Solution 3
As the chain names suggest, PREROUTING is done at first when a packet is received and is thus routed based on where it is going (destination). After all other routing rules have been applied, the POSTROUTING chain will determine where it goes based on where it came from (source).
For example, on my server, incoming ports that are to be forwarded (NATed) are all defined in the PREROUTING chain as DNAT, and all packets that come from the NATed interfaces, go through the POSTROUTING chain as SNAT, and consequently (in this case), go through the filter FORWARD chain.
Solution 4
One else nice schematic in ASCII that might help to figure out how does it work, it is handy for beginners to have it in console when working with iptables rules:
#
# (PACKET IN)->-[PREROUTING]->- ->----------->-[FORWARD]->------------>- ->-[POSTROUTING]->-(PACKET OUT)
# -mangle | -mangle | -mangle
# -nat (dst) | -filter | -nat (src)
# | |
# ->-[INPUT]->-(APPLICATION)->-[OUTPUT]->-
# -mangle -mangle
# -filter -filter
# -nat (dst)
#
(* Edited, considering the comments below...)
Related videos on Youtube
comeback4you
Updated on September 18, 2022Comments
-
 comeback4you over 1 year
comeback4you over 1 yearWhy does
SNAT(modifies source IP and/or ports) happen innattablePOSTROUTINGchain, i.e after routing? And why doesDNAT(modifies destination IP ant/or ports) happen inPREROUTINGchain? I guess latter is because there might be multiple NICs in PC with different private networks and PC does not know how to route packet if destination IP address is still publickly routable address? However, forSNATI can not see a reason why this couldn't take place inPREROUTING. -
 comeback4you almost 8 yearsYes, but is this important? I mean you would do
comeback4you almost 8 yearsYes, but is this important? I mean you would doDNATonly in case the PC acts as a router and at least one of the LAN networks use private IP addresses. -
 comeback4you almost 8 yearsIndeed, good points! So
comeback4you almost 8 yearsIndeed, good points! SoSNATcouldn't happen inPREROUTINGchain because this would mean that all the packets getSNAT-ed while actually this would be desired only for example for Internet facing interface? AndDNATneeds to happen inPREROUTINGbecause destination IP is changed and thus it needs to happen before routing decision in order to be routed via correct (LAN-facing) interface? -
Aaron D. Marasco almost 8 yearsIt's important because you asked why you can't do
SNATinpreroutingand I answered - packets whose source is the local machine never visit that table. That's why it can't. -
 comeback4you almost 8 yearsOk, but in which scenario would you do
comeback4you almost 8 yearsOk, but in which scenario would you doSNATfor a traffic coming from the local machine? For example let's say that there is PC witheth1facing LAN(IP address 10.10.10.1/24) andeth0facing Internet(IP address 198.51.100.1/24)- all the traffic going out from this machine to Internet will simply use 198.51.100.1 as a source IP address and noSNATis needed. IMHOSNATis needed only in case traffic flows through the PC and then it goes through thePREROUTING. Or am I missing something? -
AdminBee about 3 yearsWelcome to the site, and thank you for your contribution. Please note that link-only answers are discouraged, as the link may become invalid or the linked content change. Please edit your answer to include at least a summary of the linked explanation.

![IPTABLES [PART-1] : "UNDERSTANDING THE CONCEPT"](https://i.ytimg.com/vi/vbhr4csDeI4/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLBovKYd5heeT0eQFP4enqBJ_GCa1Q)