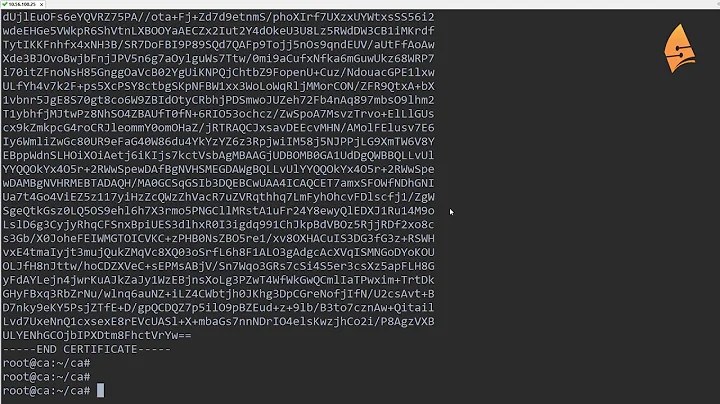
Windows CA to issue certificate to authenticate SSH to a Linux server
Between OpenSSH 5.4's readme and Roumen Petrov it does not appear that it is available to the extent you are looking for at this date. It also appears that OpenSSH isn't all that interested in supporting it.
That being said, you maybe able to make it happen if you install the forked version Petrov provides.
-
http://www.openssh.org/txt/release-5.4
"Add support for certificate authentication of users and hosts using a new, minimal OpenSSH certificate format (not X.509)."
-
http://www.openssh.org/features.html
"All components of a restrictive nature (i.e. patents, see ssl) have been removed from the source code; any licensed or patented components are chosen from external libraries (e.g. OpenSSL)."
- http://roumenpetrov.info/openssh/ - provides patch for current OpenSSH version which might do what you need. I can't vouch for it, but looks interesting. I'm not inclined to diverge from the main branch of OpenSSH myself, security is to important and I don't have the resources to properly verify this significant of a change.
Related videos on Youtube
BArnold
Updated on September 18, 2022Comments
-
BArnold almost 2 years
I have a Windows Server Root Certificate Authority, Linux SSH server, and users with Windows SSH clients. The Linux box is not part of the AD domain (and probably never will be [sigh])
OpenSSH 5.4 and above supports X.509 certiicate based authentication. I am trying to find a way to use my Windows Certificate Authority to issue certificates for authentication of the users when the SSH to the Linux box.
I do not want to have to generate a keypair on each user's desktop. And we want the certificates controlled and revokable at the Windows CA.
My question is not exactly the same as SSH from Windows to Linux with AD certificates (and the referenced moelinux.net seems to be down)
I have searched Google a lot, and haven't found much results about how to accomplish this. An answer doesn't necessarily have to include a full tutorial, even some hints about what to search on or pointers to some references may be helpful.
-
 Philip almost 12 yearsSorry if it should be obvious: What's your question exactly??
Philip almost 12 yearsSorry if it should be obvious: What's your question exactly?? -
Zoredache almost 12 yearsI updated your question a bit. I hope I haven't changed it too much, but I believe my edits make it clearer what you are looking for.
-
Harry Johnston almost 12 yearsI don't think there's any way to use client SSL certificates without generating keys on the clients; if the client doesn't have a key, how is it going to prove that it owns the certificate? (However, it may be possible to get Windows to generate these keys silently on demand.)
-
Harry Johnston almost 12 yearsIt seems to me that the key component here is the SSH client. What SSH client are you using, and have you checked the documentation / vendor's web site / vendor's support forum?
-
 Cameron Kerr about 9 yearsI would suggest that you instead use a configuration management tool to manage the contents of ~/.ssh/authorized_keys on your servers. That way you can use it for server to server traffic as well as from any ssh client or ssh tool (eg. to integrate with a monitoring solution such as SCOM).
Cameron Kerr about 9 yearsI would suggest that you instead use a configuration management tool to manage the contents of ~/.ssh/authorized_keys on your servers. That way you can use it for server to server traffic as well as from any ssh client or ssh tool (eg. to integrate with a monitoring solution such as SCOM).
-