wpa_supplicant does not connect with "ioctl[SIOCSIWENCODEEXT]: Invalid argument" error!
Solution 1
First of all, I think you'll have better luck if your router is set to use WPA2-AES and not TKIP.
Second, I believe you are taking the long, complicated route when the short, easy route would work perfectly well. First, I suggest you back up your current wpa_supplicant.conf file:
sudo mv /etc/wpa_supplicant/wpa_supplicant.conf /etc/wpa_supplicant/wpa_supplicant.bak
Next, I suggest you edit /etc/network/interfaces:
auto lo
iface lo inet loopback
auto wlan0
iface wlan0 inet static
address 192.168.1.150
netmask 255.255.255.0
gateway 192.168.1.1
wpa-essid MYESSID12345
wpa-psk MYPASSWORD$1234567
Of course, substitute your details here. Restart the interface:
sudo ifdown wlan0 && sudo ifup -v wlan0
Test:
ping -c3 www.ubuntu.com
If you get ping results, you are connected.
Solution 2
I ran into this today as well. I pulled out a wpa_supplicant.conf file that has worked for me in the past on my Raspberry Pi devices and used it here. Once I tried with this file, my wpa_supplicant was consistently connecting.
I took some time today to try and disable some of the network= sections to try and narrow down which one section was applicable for my wireless network, but I gave up after a while. Taking out and putting back individual sections seemed to be narrowing things down, but then I don't know why it still wasn't connecting, so I gave up and put the whole thing back in there and got myself a DHCP IP address from my router.
Here was the /etc/wpa_supplicant/wpa_supplicant.conf file I used:
network={
ssid="MYESSID12345"
scan_ssid=1
psk="MYPASSWORD$1234567"
proto=RSN
key_mgmt=WPA-PSK
pairwise=CCMP
auth_alg=OPEN
priority=999
}
network={
ssid="MYESSID12345"
psk="MYPASSWORD$1234567"
proto=RSN
key_mgmt=WPA-PSK
pairwise=CCMP
auth_alg=OPEN
priority=99
}
network={
ssid="MYESSID12345"
scan_ssid=1
key_mgmt=NONE
priority=2
}
network={
ssid="MYESSID12345"
psk="MYPASSWORD$1234567"
proto=RSN
key_mgmt=WPA-PSK
pairwise=CCMP
auth_alg=OPEN
priority=-1
}
With this, I ran:
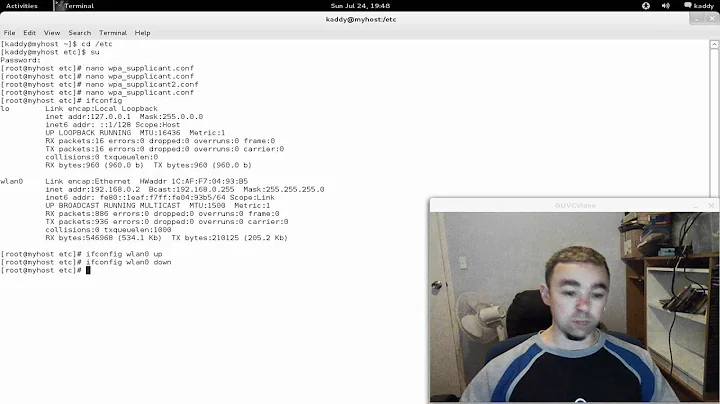
$ sudo -i
# cd /etc/wpa_supplicant
# wpa_supplicant -Dwext -i wlp1s0 -c wpa_supplicant.conf
Successfully initialized wpa_supplicant
ioctl[SIOCSIWENCODEEXT]: Invalid argument
ioctl[SIOCSIWENCODEEXT]: Invalid argument
...
wlp1s0: CTRL-EVENT-CONNECTED - Connection to ... completed [id=0 id_str=]
I still got the same errors in stdout, but things still looked better and more info in /var/log/syslog than before.
After this in a separate console:
# dhclient -v -r wlp1s0
# dhclient -v wlp1s0
I got my IP address and so I was able to proceed:
$ ping 8.8.8.8
Related videos on Youtube
PHP Learner
I decided to create a web site of my self, using PHP language. While learning PHP, I became familiar with Linux and Ubuntu and find it better than Microsoft Windows. Now trying to learn both PHP and Linux (Ubuntu) simultaneously.
Updated on September 18, 2022Comments
-
PHP Learner over 1 year
Ubuntu Server 12.04 is installed on my desktop system (in text-mode, no X-Window is available) and I have no wired Ethernet connected, just wireless network is available. I use TP-Link TL-WN723N USB wireless adapter to connect to wireless network.
At first, tried to use
iwconfigto connect, but found that it could not be used to connect to a WPA2 secured network! At fisrt,iwconfigshows:lo no wireless extensions. eth0 no wireless extensions. wlan0 IEEE 802.11bgn ESSID:off/any Mode:Managed Access Point: Not-Associated Tx-Power=20 dBm Retry long limit:7 RTS thr=2347 B Fragment thr:off Power Management:offand
sudo iwlist wlan0 scanningshows:wlan0 Interface doesn't support scanning : Network is downafter running
sudo ifconfig wlan0 up,sudo iwlist wlan0 scanningshows:wlan0 Scan completed : Cell 01 - Address: OO:OO:OO:OO:OO:OO Channel:1 Frequency:2.412 GHz (Channel 1) Quality=66/70 Signal level=-44 dBm Encryption key:on ESSID:"MYESSID12345" Bit Rates:1 Mb/s; 2 Mb/s; 5.5 Mb/s; 11 Mb/s; 6 Mb/s 9 Mb/s; 12 Mb/s; 18 Mb/s Bit Rates:24 Mb/s; 36 Mb/s; 48 Mb/s; 54 Mb/s Mode:Master Extra:tsf=0000000789abcdef Extra: Last beacon: 32ms ago IE: Unknown: 000123456789ABCEDF0123456789 IE: Unknown: 0123456789ABCDEF0123 IE: Unknown: 012345 IE: Unknown: ABCEDF IE: Unknown: 0123456789AB IE: IEEE 802.11i/WPA2 Version 1 Group Cipher : TKIP Pairwise Ciphers (1) : TKIP Authentication Suites (1) : PSKI installed
wpasupplicantto connect to wireless network secured with WPA2. But there are some problems using this package:I tried following instructions in This answer
wpa_passphrase 'MYESSID12345' 'MYPASSWORD$1234567' > CONFIG_FILEafter above command, I edited CONFIG_FILE (
/etc/wpa_supplicant/wpa_supplicant.conf) so it contains:network={ ssid="MYESSID12345" scan_ssid=1 key_mgmt=WPA-PSK psk="MYPASSWORD$1234567" proto=RSN WPA pairwise=CCMP TKIP group=CCMP TKIP #psk=1234567890abcdef1234567890abcdef1234567890abcedf1234567890abcdef }Next i run
wpa_supplicant -iwlan0 -c/etc/wpa_supplicant.conf -Dwext -dd. The result is following errors onstderr:ioctl[SIOCSIWENCODEEXT]: Invalid argument ioctl[SIOCSIWENCODEEXT]: Invalid argument ioctl[SIOCSIWENCODEEXT]: Invalid argument ioctl[SIOCSIWENCODEEXT]: Invalid argumentand
stdoutis:Initializing interface 'wlan0' conf '/etc/wpa_supplicant/wpa_supplicant.conf' driver 'wext' ctrl_interface 'N/A' bridge 'N/A' Configuration file '/etc/wpa_supplicant/wpa_supplicant.conf' -> '/etc/wpa_supplicant/wpa_supplicant.conf' Reading configuration file '/etc/wpa_supplicant/wpa_supplicant.conf' Line: 1 - start of a new network block ssid - hexdump_ascii(len=12): 01 23 45 67 89 ab cd ef 01 23 45 67 MYESSID12345 scan_ssid=1 (0x1) key_mgmt: 0x2 PSK (ASCII passphrase) - hexdump_ascii(len=18): [REMOVED] proto: 0x3 pairwise: 0x18 group: 0x18 PSK (from passphrase) - hexdump(len=32): [REMOVED] Priority group 0 id=0 ssid='MYESSID12345' WEXT: cfg80211-based driver detected SIOCGIWRANGE: WE(compiled)=22 WE(source)=21 enc_capa=0xf capabilities: key_mgmt 0xf enc 0xf flags 0x0 netlink: Operstate: linkmode=1, operstate=5 Own MAC address: mm:mm:mm:mm:mm:mm wpa_driver_wext_set_key: alg=0 key_idx=0 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=1 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=2 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=3 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=4 set_tx=0 seq_len=0 key_len=0 Driver did not support SIOCSIWENCODEEXT wpa_driver_wext_set_key: alg=0 key_idx=5 set_tx=0 seq_len=0 key_len=0 Driver did not support SIOCSIWENCODEEXT wpa_driver_wext_set_countermeasures RSN: flushing PMKID list in the driver Setting scan request: 0 sec 100000 usec WPS: UUID based on MAC address - hexdump(len=16): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef EAPOL: SUPP_PAE entering state DISCONNECTED EAPOL: Supplicant port status: Unauthorized EAPOL: KEY_RX entering state NO_KEY_RECEIVE EAPOL: SUPP_BE entering state INITIALIZE EAP: EAP entering state DISABLED EAPOL: Supplicant port status: Unauthorized EAPOL: Supplicant port status: Unauthorized Added interface wlan0 RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b06 len=8 RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b1a len=8 State: DISCONNECTED -> SCANNING Scan SSID - hexdump_ascii(len=12): 01 23 45 67 89 ab cd ef 01 23 45 67 MYESSID12345 Starting AP scan for specific SSID(s) Scan requested (ret=0) - scan timeout 5 seconds RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b19 len=8 Received 656 bytes of scan results (2 BSSes) BSS: Start scan result update 1 BSS: Add new id 0 BSSID OO:OO:OO:OO:OO:OO SSID 'MYESSID12345' BSS: Add new id 1 BSSID 11:11:11:11:11:11 SSID 'OTHER1' New scan results available Selecting BSS from priority group 0 Try to find WPA-enabled AP 0: OO:OO:OO:OO:OO:OO ssid='MYESSID12345' wpa_ie_len=0 rsn_ie_len=20 caps=0x11 selected based on RSN IE selected WPA AP OO:OO:OO:OO:OO:OO ssid='MYESSID12345' Request association: reassociate: 0 selected: OO:OO:OO:OO:OO:OO bssid: 00:00:00:00:00:00 pending: 00:00:00:00:00:00 wpa_state: SCANNING Trying to associate with OO:OO:OO:OO:OO:OO (SSID='MYESSID12345' freq=2412 MHz) FT: Stored MDIE and FTIE from (Re)Association Response - hexdump(len=0): Cancelling scan request WPA: clearing own WPA/RSN IE Automatic auth_alg selection: 0x1 RSN: PMKSA cache search - network_ctx=(nil) try_opportunistic=1 RSN: Search for BSSID OO:OO:OO:OO:OO:OO RSN: Consider OO:OO:OO:OO:OO:OO for OKC RSN: No PMKSA cache entry found RSN: using IEEE 802.11i/D9.0 WPA: Selected cipher suites: group 8 pairwise 8 key_mgmt 2 proto 2 WPA: clearing AP WPA IE WPA: set AP RSN IE - hexdump(len=22): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab WPA: using GTK TKIP WPA: using PTK TKIP WPA: using KEY_MGMT WPA-PSK WPA: not using MGMT group cipher WPA: Set own WPA IE default - hexdump(len=22): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab No keys have been configured - skip key clearing State: SCANNING -> ASSOCIATING wpa_driver_wext_set_operstate: operstatioctl[SIOCSIWFREQ]: Device or resource busy e 0->0 (DORMANT) netlink: Operstate: linkmode=-1, operstate=5 wpa_driver_wext_associate wpa_driver_wext_set_drop_unencrypted wpa_driver_wext_set_psk Association request to the driver failed Setting authentication timeout: 10 sec 0 usec EAPOL: External notification - EAP success=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - EAP fail=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - portControl=Auto EAPOL: Supplicant port status: Unauthorized RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b1a len=8 RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b06 len=8 RTM_NEWLINK: operstate=0 ifi_flags=0x1003 ([UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b1a len=20 RTM_NEWLINK: operstate=0 ifi_flags=0x11003 ([UP][LOWER_UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added RTM_NEWLINK: operstate=0 ifi_flags=0x11003 ([UP][LOWER_UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8c08 len=24 AssocResp IE wireless event - hexdump(len=16): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef RTM_NEWLINK: operstate=0 ifi_flags=0x11003 ([UP][LOWER_UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added Wireless event: cmd=0x8b15 len=20 Wireless event: new AP: OO:OO:OO:OO:OO:OO Association info event resp_ies - hexdump(len=16): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef FT: Stored MDIE and FTIE from (Re)Association Response - hexdump(len=0): State: ASSOCIATING -> ASSOCIATED wpa_driver_wext_set_operstate: operstate 0->0 (DORMANT) netlink: Operstate: linkmode=-1, operstate=5 Associated to a new BSS: BSSID=OO:OO:OO:OO:OO:OO No keys have been configured - skip key clearing Associated with OO:OO:OO:OO:OO:OO WPA: Association event - clear replay counter RSN: PMKSA cache search - network_ctx=0x9c8e950 try_opportunistic=0 RSN: Search for BSSID OO:OO:OO:OO:OO:OO RSN: No PMKSA cache entry found WPA: Clear old PTK EAPOL: External notification - portEnabled=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - portValid=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - EAP success=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - portEnabled=1 EAPOL: SUPP_PAE entering state CONNECTING EAPOL: SUPP_BE entering state IDLE Setting authentication timeout: 10 sec 0 usec Cancelling scan request RX EAPOL from OO:OO:OO:OO:OO:OO RX EAPOL - hexdump(len=99): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 Setting authentication timeout: 10 sec 0 usec IEEE 802.1X RX: version=1 type=3 length=95 EAPOL-Key type=2 key_info 0x89 (ver=1 keyidx=0 rsvd=0 Pairwise Ack) key_length=32 key_data_length=0 replay_counter - hexdump(len=8): 00 00 00 00 00 00 00 01 key_nonce - hexdump(len=32): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef key_iv - hexdump(len=16): 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 key_rsc - hexdump(len=8): 00 00 00 00 00 00 00 00 key_id (reserved) - hexdump(len=8): 00 00 00 00 00 00 00 00 key_mic - hexdump(len=16): 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 WPA: RX EAPOL-Key - hexdump(len=99): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 State: ASSOCIATED -> 4WAY_HANDSHAKE WPA: RX message 1 of 4-Way Handshake from OO:OO:OO:OO:OO:OO (ver=1) RSN: msg 1/4 key data - hexdump(len=0): WPA: Renewed SNonce - hexdump(len=32): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef WPA: PTK derivation - A1=mm:mm:mm:mm:mm:mm A2=OO:OO:OO:OO:OO:OO WPA: PMK - hexdump(len=32): [REMOVED] WPA: PTK - hexdump(len=64): [REMOVED] WPA: WPA IE for msg 2/4 - hexdump(len=22): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab WPA: Sending EAPOL-Key 2/4 WPA: TX EAPOL-Key - hexdump(len=121): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 RX EAPOL from OO:OO:OO:OO:OO:OO RX EAPOL - hexdump(len=161): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef IEEE 802.1X RX: version=1 type=3 length=157 EAPOL-Key type=2 key_info 0x13c9 (ver=1 keyidx=0 rsvd=0 Pairwise Install Ack MIC Secure Encr) key_length=32 key_data_length=62 replay_counter - hexdump(len=8): 00 00 00 00 00 00 00 02 key_nonce - hexdump(len=32): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef key_iv - hexdump(len=16): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef key_rsc - hexdump(len=8): 00 00 00 00 00 00 00 00 key_id (reserved) - hexdump(len=8): 00 00 00 00 00 00 00 00 key_mic - hexdump(len=16): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef WPA: RX EAPOL-Key - hexdump(len=161): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef RSN: encrypted key data - hexdump(len=62): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab WPA: decrypted EAPOL-Key key data - hexdump(len=62): [REMOVED] State: 4WAY_HANDSHAKE -> 4WAY_HANDSHAKE WPA: RX message 3 of 4-Way Handshake from OO:OO:OO:OO:OO:OO (ver=1) WPA: IE KeyData - hexdump(len=62): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab WPA: RSN IE in EAPOL-Key - hexdump(len=22): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab WPA: GTK in EAPOL-Key - hexdump(len=40): [REMOVED] WPA: Sending EAPOL-Key 4/4 WPA: TX EAPOL-Key - hexdump(len=99): 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 01 23 45 67 89 ab cd ef 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 WPA: Installing PTK to the driver. wpa_driver_wext_set_key: alg=2 key_idx=0 set_tx=1 seq_len=6 key_len=32 EAPOL: External notification - portValid=1 State: 4WAY_HANDSHAKE -> GROUP_HANDSHAKE RSN: received GTK in pairwise handshake - hexdump(len=34): [REMOVED] WPA: Group Key - hexdump(len=32): [REMOVED] WPA: Installing GTK to the driver (keyidx=1 tx=0 len=32). WPA: RSC - hexdump(len=6): 00 00 00 00 00 00 wpa_driver_wext_set_key: alg=2 key_idx=1 set_tx=0 seq_len=6 key_len=32 WPA: Key negotiation completed with OO:OO:OO:O:OO:OO [PTK=TKIP GTK=TKIP] Cancelling authentication timeout State: GROUP_HANDSHAKE -> COMPLETED CTRL-EVENT-CONNECTED - Connection to OO:OO:OO:OO:OO:OO completed (auth) [id=0 id_str=] wpa_driver_wext_set_operstate: operstate 0->1 (UP) netlink: Operstate: linkmode=-1, operstate=6 EAPOL: External notification - portValid=1 EAPOL: External notification - EAP success=1 EAPOL: SUPP_PAE entering state AUTHENTICATING EAPOL: SUPP_BE entering state SUCCESS EAP: EAP entering state DISABLED EAPOL: SUPP_PAE entering state AUTHENTICATED EAPOL: Supplicant port status: Authorized EAPOL: SUPP_BE entering state IDLE EAPOL authentication completed successfully RTM_NEWLINK: operstate=1 ifi_flags=0x11043 ([UP][RUNNING][LOWER_UP]) RTM_NEWLINK, IFLA_IFNAME: Interface 'wlan0' added EAPOL: startWhen --> 0 EAPOL: disable timer tick CTRL-EVENT-TERMINATING - signal 2 received Removing interface wlan0 wpa_driver_wext_deauthenticate wpa_driver_wext_set_key: alg=0 key_idx=0 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=1 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=2 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=3 set_tx=0 seq_len=0 key_len=0 wpa_driver_wext_set_key: alg=0 key_idx=4 set_tx=0 seq_len=0 key_len=0 Driver did not support SIOCSIWENCODEEXT wpa_driver_wext_set_key: alg=0 key_idx=5 set_tx=0 seq_len=0 key_len=0 Driver did not support SIOCSIWENCODEEXT wpa_driver_wext_set_key: alg=0 key_idx=0 set_tx=0 seq_len=0 key_len=0 State: COMPLETED -> DISCONNECTED wpa_driver_wext_set_operstate: operstate 1->0 (DORMANT) netlink: Operstate: linkmode=-1, operstate=5 EAPOL: External notification - portEnabled=0 EAPOL: SUPP_PAE entering state DISCONNECTED EAPOL: Supplicant port status: Unauthorized EAPOL: SUPP_BE entering state INITIALIZE EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - portValid=0 EAPOL: Supplicant port status: Unauthorized EAPOL: External notification - EAP success=0 EAPOL: Supplicant port status: Unauthorized wpa_driver_wext_set_countermeasures No keys have been configured - skip key clearing BSS: Remove id 0 BSSID OO:OO:OO:OO:OO:OO SSID 'MYESSID12345' BSS: Add new id 1 BSSID 11:11:11:11:11:11 SSID 'OTHER1' Cancelling scan request Cancelling authentication timeout netlink: Operstate: linkmode=0, operstate=6after the last command,
wlan0goes DOWN and I have to make it up usingsudo iwconfig wlan0 upcommand again. Also I tried removingnetwork-managerpackage based on a comment saying this may solve the problem, but no success.Also tried to edit
wpa_supplicant.conf1file as follows:TRY #1 for
wpa_supplicant.confnetwork={ ssid="MYESSID12345" #psk="MYPASSWORD$1234567" psk=1234567890abcdef1234567890abcdef1234567890abcedf1234567890abcdef }TRY #2 for
wpa_supplicant.confnetwork={ ssid="MYESSID12345" scan_ssid=1 key_mgmt=WPA-PSK #psk="MYPASSWORD$1234567" proto=RSN WPA pairwise=CCMP TKIP group=CCMP TKIP psk=1234567890abcdef1234567890abcdef1234567890abcedf1234567890abcdef }-
numand almost 9 yearsCould you try to connect with nl80211 driver? Use 'wpa_supplicant -B -i wlan0 -c /etc/wpa_supplicant.conf -D nl80211' command. Also, did you install firmware for this driver?
-
PHP Learner almost 9 yearsI tried removing
#psk="MYPASSWORD$1234567"from mywpa_supplicant.conffile (TRY#1) and the problem has solved (wpa_supplicantconnected to my AP and after runningsudo dhclient wlan0I could access Internet). After that I recreated the CONFIG_FILE usingwpa_passphrase 'MYESSID12345' 'MYPASSWORD$1234567' > CONFIG_FILEcommand and it creates a new CONFIG_FILE same as TRY #1 and the problem did not occurred again!
-
-
 pospi over 7 yearsThe problem with this approach though, is that in bypassing wpa_supplicant your PC won't reconnect to the wifi if connection is lost.
pospi over 7 yearsThe problem with this approach though, is that in bypassing wpa_supplicant your PC won't reconnect to the wifi if connection is lost. -
arn-arn about 7 yearsthanks so much... i wasted one day but when i applied your answer it worked...
-
 lightsout over 6 yearsCan I copy your address netmask and gateway values? If not what do I put in there?
lightsout over 6 yearsCan I copy your address netmask and gateway values? If not what do I put in there? -
 chili555 over 6 years@lightsout I think this a complex question and I recommend that you start your own. I’ll be happy to help.
chili555 over 6 years@lightsout I think this a complex question and I recommend that you start your own. I’ll be happy to help. -
 chili555 over 6 yearsOr you can reboot. I think the 'down' part can safely be ignored. Did the 'up' part seen to connect?
chili555 over 6 yearsOr you can reboot. I think the 'down' part can safely be ignored. Did the 'up' part seen to connect? -
 lightsout over 6 years@chili555 I want to try this script on a different computer but the wlan0 on that computer is called wlp2s0 instead, will this still work?
lightsout over 6 years@chili555 I want to try this script on a different computer but the wlan0 on that computer is called wlp2s0 instead, will this still work? -
 chili555 over 6 years@lightsout A new question, please.
chili555 over 6 years@lightsout A new question, please. -
Chris about 6 yearsI spent an entire day fiddling with wpa_supplicant. Then I tried this and it worked. Linux in a nutshell ...
-
 Dave Nottage about 6 yearsI'm still struggling. Using a static or dhcp address, it seems to refuse to connect. The SSID I'm using has spaces in it, however both using quotes around it and not using quotes does not work. Am I supposed to use the value generated by wpa_passphrase for the wpa-psk value? Either way i.e using that, or using plain text does not work (the password has no spaces)
Dave Nottage about 6 yearsI'm still struggling. Using a static or dhcp address, it seems to refuse to connect. The SSID I'm using has spaces in it, however both using quotes around it and not using quotes does not work. Am I supposed to use the value generated by wpa_passphrase for the wpa-psk value? Either way i.e using that, or using plain text does not work (the password has no spaces) -
 chili555 about 6 years@DaveNottage I suggest that you start your own new question and show your file. The wpa-psk should be in clear text. It should, of course, be disguised in your question.
chili555 about 6 years@DaveNottage I suggest that you start your own new question and show your file. The wpa-psk should be in clear text. It should, of course, be disguised in your question. -
 Dave Nottage about 6 years@chili555 Thanks for the very speedy reply, however it turns out I needed to install a package for the firmware (an alternative manual install apparently doesn't cut it). All good now, using your answer here!
Dave Nottage about 6 years@chili555 Thanks for the very speedy reply, however it turns out I needed to install a package for the firmware (an alternative manual install apparently doesn't cut it). All good now, using your answer here!