Cisco ASA: Allow established traffic back in
Solution 1
Last time I checked, you don't need to define a rule when crossing from a high security zone (100) to a lower security zone, it's permitted by default.
That being said, you'll want to look at the established documentation. Also doesn't hurt to take a quick look at the security-level docs either.
Solution 2
The ASA is stateful by default. If you allow the traffic out (either by security-level processing or by ACL) it will automatically allow the return traffic back through.
I would be inclined to believe you are actually running into a nat-control issue. Nat-control enforces the use of NAT, which is to say, if nat-control is enabled, any traffic traversing firewall interfaces MUST be NATed or it gets dropped. In 8.2 code, nat-control is enabled by default.
Since you mention you are not doing NAT on your Firewall, you will also have to disable nat-control by using the command no nat-control from global configuration. That, or configure NAT Exemptions to instruct your firewall to not NAT your traffic, while still satisfying nat-control.
To check if it is enabled: show run nat-control
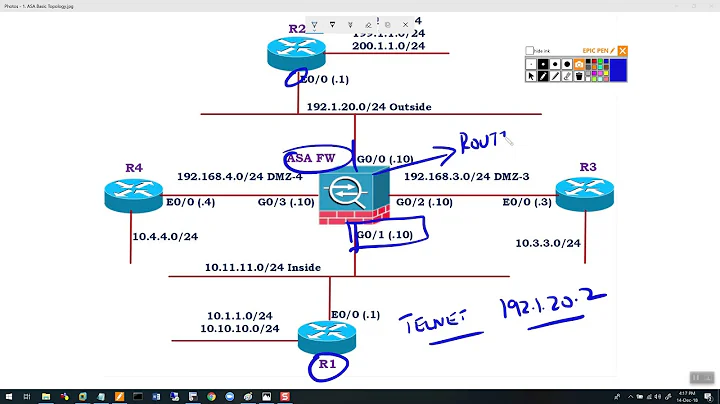
Related videos on Youtube
Comments
-
DrStalker over 1 year
I have a Cisco ASA 5505 (ver 8.2(2)) with two interfaces; inside (security level 100) and outside (security level 50). There is one subnet on inside, 10.1.1.0/24.
There is no NAT for traffic moving from inside to outside; that is handled by an upstream router.
I want to configure the firewall so that any system on the inside interface can initiate a connection to the outside world and receive the return traffic but the outside world cannot initiate connections to the inside systems. Letting the traffic out is easy:
access-list inside_in extended permit IP 10.1.1.0 255.255.255.0 anybut what do I need to configure on the ASA to let the responses back in without opening the firewall to all traffic? normally this is handled by NAT, but in this case I do not want to use NAT.
-
DrStalker almost 14 yearsPerfect: the following three lines have everything we need working: established tcp 0 0 established udp 0 0 access-list outside_in extended permit icmp any any echo-reply The allow-inside-out rule is there due to force of habit, as well as my dislike of trusting default settings that don't get displayed in configs. :-)