How do I prevent libvirt from adding iptables rules for guest NAT networks?
Solution 1
Well I've found an answer that suits me: I've gone back to school and learned to do it the old fashioned way. No need to use libvirt's fancy networking functions as I can just:
- set up my own bridged network(s) (not attached to any physical network port)
- use a DHCP server on the host and masquerade in iptables
- edit the libvirt guest config files to use the bridge(s)
- have complete flexibility in how I want to configure security with iptables
Solution 2
It is not possible to modify these rules, since they are not in a configuration file or a script, but in the sourcecode.
But in 2016 the "open"-network "forward mode" was added. When specified for a network, libvirt does not generate any iptables rules for the network. See bug 846810.
So edit your network (virsh net-edit) to <forward mode='open'/>.
open is like route, but there will be no firewall rules added to either enable or prevent any of this traffic.
See Network XML format for more details.
Solution 3
First, it is already possible to avoid the iptables rules - simply do not request a NAT based virtual network. The 'default' virtual network is intentionally NAT based. You are free to remove this & default one which doesn't provide NAT.
So to avoid the cron job:
virsh net-destroy default
virsh net-undefine default
Of course, as @user83664 wrote, you'll have to use either a bridge or hostonly networks going forward.
Related videos on Youtube
Admin
Updated on September 18, 2022Comments
-
 Admin almost 2 years
Admin almost 2 yearsSimilar to this old request on BugZilla for Fedora 8, I'm hoping something has changed since then or someone knows another way.
I want to manage the iptables rules by hand—the one-size-fits-all automatic rules don't suit me at all. These rules seem to be added and removed when a network is started and destroyed. Is there a way of either preventing these rules being added at all or hooking a script into the network start that restores the default rules afterwards.
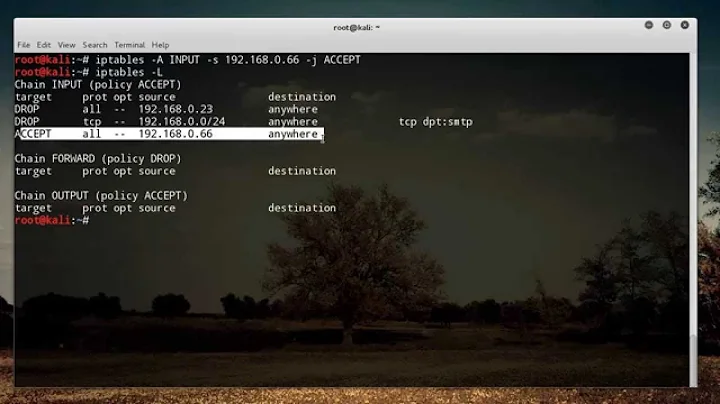
For now, I'm using a very crude method with
cron, but I hope there is a better way:* * * * * root iptables-restore < /etc/sysconfig/iptables-
Nils over 11 yearsIs KVM using a modular script to start virtual network devices? If so you could manipulate that script (this is how I would do this on XEN).
-
 Admin over 11 yearsI don't think so but tbh I'm not sure how to find out.
Admin over 11 yearsI don't think so but tbh I'm not sure how to find out. -
David Corsalini over 11 yearsThe best place to ask is the libvirt devel list or on their IRC channel (#virt on OFTC)
-
-
David Corsalini over 11 years+1 just use bridged mode, or move on to 802.1Qbg/h