How to log commands/logins in linux?
Solution 1
Root is root. Anything you do to try to keep track of root usage can be subverted or circumvented by someone who has root; even if you cause bash to pipe all history file entries to syslog on a secured remote server, for example, your system is only safe until the badly-behaved user figures out what you've done and disables or works around it.
This is a social problem, not a technical one. You need to implement a policy that will prevent people from using root, and put in place system checks to ensure that only acceptable access is granted, in a monitored and logged environment.
- Reconfigure sshd to deny root SSH login.
- Change the root password.
- Configure sudo/sudoers to allow each user only the privileged access they require.
Hope this helps - good luck.
Solution 2
well you could just send yourself an email saying that "Elvis" entered the building
In the .bashrc put this
echo 'ALERT - Root Shell Access (YOURSERVERNAME) on:' `date` `who` | mail -s "Alert: Root Access from `who | cut -d"(" -f2 | cut -d")" -f1`" YOUREMAIL
So every time the user root logs in you will be notified
Solution 3
The following version of OpenSSH allows you to monitor all keystrokes which pass through the SSH daemon. My organization (Lawrence Berkeley National Laboratory) uses this code internally to support our science research environments, with great success.
https://github.com/set-element/openssh-hpn-isshd
A version of OpenSSH designed for high security installations where it is desirable to audit user activity. To do this we modify the SSH daemon to export information about user names, authentication, keystrokes, file transfers, remote command execution and a variety of SSH related metadata in as agnostic a way as possible. As an addition to this project, we provide infrastructure via the Bro Intrusion Detection System. The most general idea here is that a site can generate local security policy in the Bro scripting language and monitor in near real time user activity.
Solution 4
BSM audit logs will help in tracking user commands and events
http://seclab.cs.ucdavis.edu/projects/misuse/prototypes/bsm.html
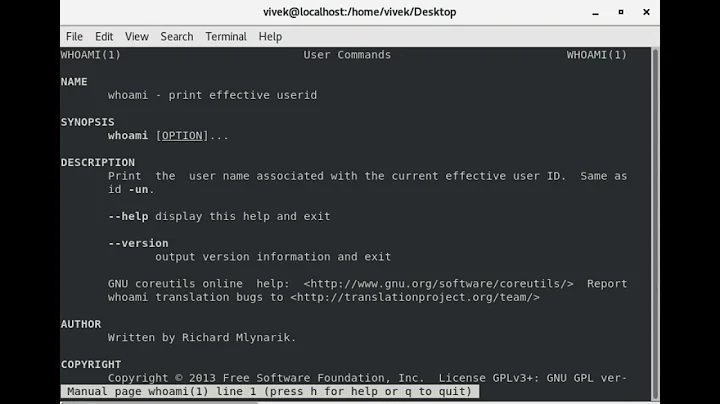
whowatch tool is also helpfull
http://www.cyberciti.biz/tips/linux-and-unix-interactive-process-and-users-monitoring-tool.html
Related videos on Youtube
Admin
Updated on September 18, 2022Comments
-
 Admin over 1 year
Admin over 1 yearI'm feeling that some people are using the root, how i can log all commands and connections times including ips made to the server (ssh) from all users?
history command is not enough
-
0xC0000022L about 13 years
/var/log/auth.logand/var/log/daemon.log...? What you want logged should already be logged in most vanilla setups. So you need to filter it out of the logs, that's all. Specifically if you'd use sudo, you will also see which command was issues. Also, I would not recommend to allow root login via SSH.
-
-
DerfK about 13 yearsThis is pretty much the only way. With permission to do anything, you can log every command the user runs and still never figure out what happened if they
vi script.sh; chmod +x script.sh; ./script.sh; rm script.sh. -
jouell almost 7 yearssounds nice but it's deprecated when I visit the page
-
Stefan Lasiewski almost 7 years@jouell Thanks for that notice. I updated the link.
-
 yukashima huksay over 6 yearsThis is a good answer but I think bashrc is not called on ssh login. But I guess bash.profile is called so then you should source bashrc from bash.profile.
yukashima huksay over 6 yearsThis is a good answer but I think bashrc is not called on ssh login. But I guess bash.profile is called so then you should source bashrc from bash.profile.