Login with SSH public key doesn't work
/home/serveruser/.ssh/authorized_keys should be a file.
You create it by adding the contents of id_rsa.pub to it (i.e. cat /home/homeuser/.ssh/id_rsa.pub >> authorized_keys).
(Obviously you have to copy the public key to the server first.)
Related videos on Youtube
The Quantum Physicist
Updated on September 18, 2022Comments
-
The Quantum Physicist over 1 year
So I have my home computer, and my server. I'm trying to login to my server with my private key.
On my server say I have the user
serveruser, to which I login from my home computer usingssh -Y [email protected]And at my home computer, I have the user
homeuseron my home computer.So now, I want to login to the server using my private key. For that, I already have a key with passphrase in
/home/homeuser/.ssh/. So I took the public key (id_rsa.pub), and copied it to my server at/home/serveruser/.ssh/authorized_keys.Now I would like to login using that key, so I tried to login using
ssh -Y [email protected]and it still asks me for the password, and not the passphrase.
I tried also logging in using
ssh -i /home/homeuser/.ssh/id_rsa -Y [email protected]and I'm still being asked for the user password.
What did I do wrong? Please advise.
Thank you for any efforts.
EDIT: According to Mason Heller's recommendation, I executed ssh-add, but it still insists that I input the password for [email protected].
EDIT: Information from
ssh -v -Y myserver.com(personal information modified for anonymity).OpenSSH_5.9p1 Debian-5ubuntu1.1, OpenSSL 1.0.1 14 Mar 2012 debug1: Reading configuration data /etc/ssh/ssh_config debug1: /etc/ssh/ssh_config line 19: Applying options for * debug1: Connecting to myserver.com [100.100.100.100] port 22. debug1: Connection established. debug1: identity file /home/homeuser/.ssh/id_rsa type 1 debug1: Checking blacklist file /usr/share/ssh/blacklist.RSA-2048 debug1: Checking blacklist file /etc/ssh/blacklist.RSA-2048 debug1: identity file /home/homeuser/.ssh/id_rsa-cert type -1 debug1: identity file /home/homeuser/.ssh/id_dsa type -1 debug1: identity file /home/homeuser/.ssh/id_dsa-cert type -1 debug1: identity file /home/homeuser/.ssh/id_ecdsa type -1 debug1: identity file /home/homeuser/.ssh/id_ecdsa-cert type -1 debug1: Remote protocol version 2.0, remote software version OpenSSH_6.0p1 Debian-4 debug1: match: OpenSSH_6.0p1 Debian-4 pat OpenSSH* debug1: Enabling compatibility mode for protocol 2.0 debug1: Local version string SSH-2.0-OpenSSH_5.9p1 Debian-5ubuntu1.1 debug1: SSH2_MSG_KEXINIT sent debug1: SSH2_MSG_KEXINIT received debug1: kex: server->client aes128-ctr hmac-md5 none debug1: kex: client->server aes128-ctr hmac-md5 none debug1: sending SSH2_MSG_KEX_ECDH_INIT debug1: expecting SSH2_MSG_KEX_ECDH_REPLY debug1: Server host key: ECDSA b2:1a:68:21:5a:72:c4:f7:ec:ea:60:12:e4:f8:b5:71 debug1: Host 'myserver.com' is known and matches the ECDSA host key. debug1: Found key in /home/homeuser/.ssh/known_hosts:11 debug1: ssh_ecdsa_verify: signature correct debug1: SSH2_MSG_NEWKEYS sent debug1: expecting SSH2_MSG_NEWKEYS debug1: SSH2_MSG_NEWKEYS received debug1: Roaming not allowed by server debug1: SSH2_MSG_SERVICE_REQUEST sent debug1: SSH2_MSG_SERVICE_ACCEPT received debug1: Authentications that can continue: publickey,password debug1: Next authentication method: publickey debug1: Offering RSA public key: /home/homeuser/.ssh/id_rsa debug1: Authentications that can continue: publickey,password debug1: Offering RSA public key: [email protected] debug1: Authentications that can continue: publickey,password debug1: Trying private key: /home/homeuser/.ssh/id_dsa debug1: Trying private key: /home/homeuser/.ssh/id_ecdsa debug1: Next authentication method: passwordMore information:
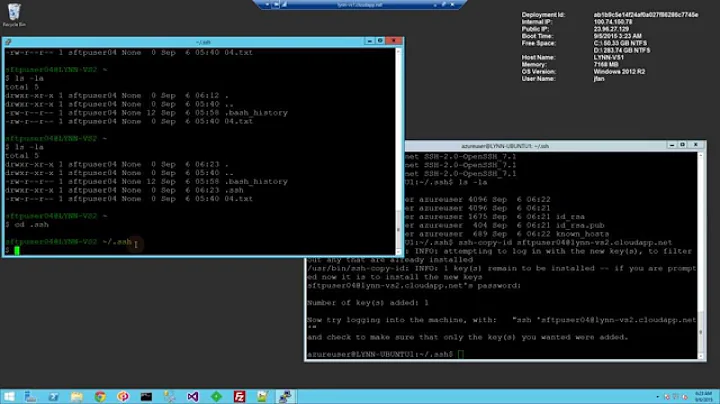
cat /home/homeuser/.ssh/id_rsa.pub
--removed for security--/home/serveruser/.ssh/authorized_keys
total 4 -rwx------ 1 serveruser serveruser 400 Jan 26 01:09 id_rsa.pubcat /home/serveruser/.ssh/authorized_keys
cat: /home/serveruser/.ssh/authorized_keys: Is a directory-
Jaap Eldering over 10 yearsYou should run
sshwith one or more options-vpassed to it, to see whether it loads your private key and tries to offer it for authentication to the server. Pasting it here may offer other people more clues to answer your question. -
The Quantum Physicist over 10 years@JonasWielicki that didn't work... please check the verbose output.
-
The Quantum Physicist over 10 years@eldering done, please check the output.
-
 Marki over 10 yearsPlease show us the following
Marki over 10 yearsPlease show us the followingcat /home/homeuser/.ssh/id_rsa.pub,ls -l /home/serveruser/.ssh/authorized_keys,cat /home/serveruser/.ssh/authorized_keys. -
The Quantum Physicist over 10 years@Marki done, please check the output.
-
 Marki over 10 yearsSee, /home/serveruser/.ssh/authorized_keys should be a file. You create it by merely adding the contents of id_rsa.pub to it (i.e.
Marki over 10 yearsSee, /home/serveruser/.ssh/authorized_keys should be a file. You create it by merely adding the contents of id_rsa.pub to it (i.e.cat /home/homeuser/.ssh/id_rsa.pub >> authorized_keys). (Obviously you have to copy the public key to the server first.) Now just having you execute those commands should have made you think whycatdidn't work ;-)
-
-
Jaap Eldering over 10 yearsAlthough
ssh-agentmakes key management easier, it is by no means necessary to allow public key authentication. Without it,sshwill by default already try to authenticate with a private key~/.ssh/id_rsaif available and ask for its passphrase if necessary. -
 Marki over 10 yearsYou need not use
Marki over 10 yearsYou need not usessh-agent. -
The Quantum Physicist over 10 yearsThank you! It works now. But it doesn't ask me for the passphrase... is that normal? I expected that it would ask me for the passphrase every time I log in. And one more question, how can I add more public keys? should I separate them with a new line?
-
 Marki over 10 yearsIf no passphrase is asked you probably already played with
Marki over 10 yearsIf no passphrase is asked you probably already played withssh-agent(make sure it doesn't run or logoff/login again). Unless you created a key without a passphrase (it will not sayProc-Type: 4,ENCRYPTEDor so when looking at the private key). And yes, you add them by adding new lines to the file. You should probably take a look atman ssh, especially the "AUTHENTICATION" section.