Linux / AD integration with SSSD: how to choose what systems a user can log into?
Solution 1
I would recommend against using the filter based access control filters for most deployments for two reasons:
- they are hard to get right
- the filters are applied on the user entry that is logging in. This might have interesting consequences especially if the filter contains a
memberofattribute while the user is a member of nested groups - since the user entry only contains memberofs to direct parents, the nested groups would never match.
For very simple use cases, such as allowing a user or a group of users, I would recommend to use the simple access provider
For complex use-cases, SSSD supports AD GPOs starting with the 1.12.x series, search the sssd-ad man page for details.
Solution 2
In your sssd.conf configuration file, you can modify the access filter to meet your needs:
Under the domain/default section, try the following:
access_provider = ldap
ldap_access_filter = memberOf=cn=GroupName,ou=Groups,dc=domain,dc=com
Solution 3
After doing some more RTFM I found the details in sssd-ad(5) - I must have missed them the first time:
- the default
access_providerispermit, so every user that can authenticate is given permission to login to the system. This is explained in sssd.conf(5). - to manage specific permissions you must set
access_provider = ad - you then use
ad_access_filteras detailed in sssd-ad(5) to define a filter for users that can login
(but I still don't know if there's any way to specify systems one by one on the AD side for a user to allow login)
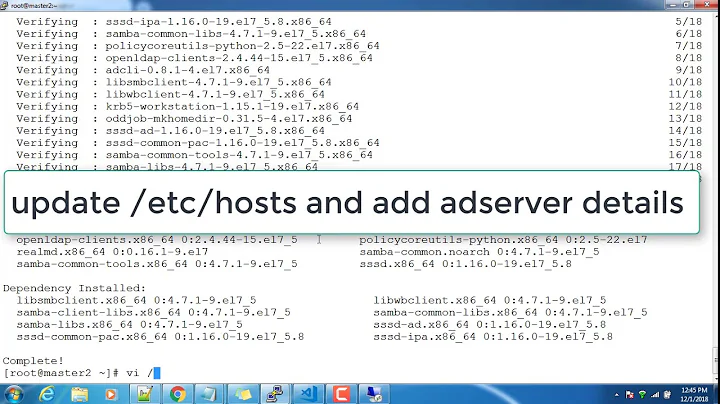
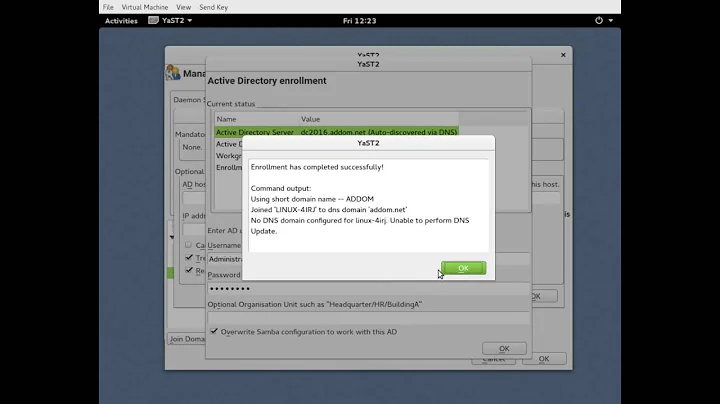
Related videos on Youtube
Luke404
Self-made sysadmin, specialized on linux systems and trying to grow my own business. Also Python coder out of passion and necessity, learning my way through OOP and frameworks and whatnot.
Updated on September 18, 2022Comments
-
Luke404 almost 2 years
We are trying out ActiveDirectory integration on some linux systems with SSSD.
So far so good we joined the linux systems to the domain and we can log into linux systems with AD-defined users. Right now every AD user can log into every Linux system which has been integrated with SSSD.
How can I let user Foo log into LinuxServer01 but prevent him to log into LinuxServer02? And/or how can I block a user to log into every linux systems and just let him on some specific ones?
-
 ewwhite over 9 yearsSome people prefer the LDAP syntax.
ewwhite over 9 yearsSome people prefer the LDAP syntax. -
jhrozek over 9 yearsPlease note that if you combine id_provider=ad and access_provider=ldap then you must also configure stuff like ldap_uri or ldap connection authentication, the configuration will note be inherited from the AD PROVIDER
-
Dmitry Donskih over 2 yearsIt should be noted that simple access provider cannot handle expired/locked accounts and trusted domains. Here is more detailed comparing from SSSD offcial website.