postfix cannot access dovecot config file
The error message explicitly tells you that the /etc/dovecot directory needs the +x permission, so that should have been the first thing you tried.
chmod +x /etc/dovecot
Related videos on Youtube
zensys
Updated on September 18, 2022Comments
-
zensys over 1 year
I do not receive email because of the below, as mentioned in my mail.log:
Sep 21 07:58:32 WWW postfix/pipe[5118]: 8F5FD605C8: to=<[email protected]>, relay=dovecot, delay=50089, delays=50089/0.04/0/0, dsn=4.3.0, status=deferred (temporary failure. Command output: lda: Error: user [email protected]: Error reading configuration: stat(/etc/dovecot/dovecot.conf) failed: Permission denied (euid=5000(vmail) egid=8(mail) missing +x perm: /etc/dovecot, we're not in group 113(dovecot), dir owned by 8:113 mode=0750) lda: Fatal: Internal error occurred. Refer to server log for more information. )I tried adding the mail and vmail users to the dovecot (113) group but no no avail.
What worked is adding read and execute access to all for the /etc/dovecot file but I consider that a workaround with possible hazards now or in the future that I cannot foresee.
What would be best practice: add another system user to the dovecot group or is there any other config which should be changed.
Note that I added a vmail user and group which own my vmail directory. These are used in my postfix virtual_uid_maps and virtual_gid_maps settings. Has the mail system user now become redundant?
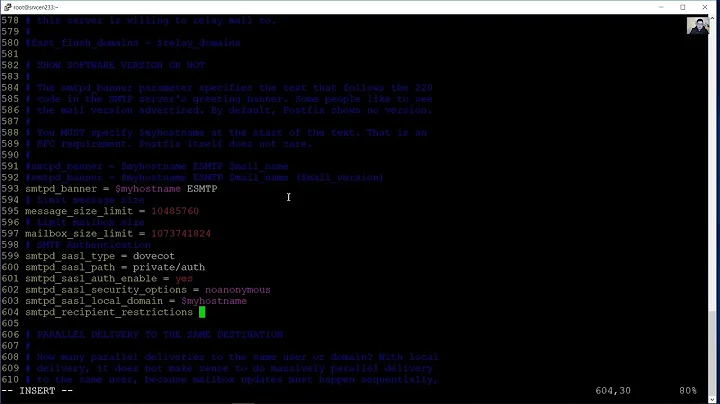
Here are my postfix and dovecot settings as well as my passwd and group files:
# See /usr/share/postfix/main.cf.dist for a commented, more complete version # The first text sent to a connecting process. smtpd_banner = $myhostname ESMTP $mail_name biff = no # appending .domain is the MUA's job. append_dot_mydomain = no readme_directory = no # alias maps # default includes nis:alias_maps which produces warning in log alias_maps = hash:/etc/aliases # SASL parameters # --------------------------------- # Use Dovecot to authenticate. smtpd_sasl_type = dovecot # Referring to /var/spool/postfix/private/auth smtpd_sasl_path = private/auth smtpd_sasl_auth_enable = yes broken_sasl_auth_clients = yes smtpd_sasl_security_options = noanonymous smtpd_sasl_local_domain = smtpd_sasl_authenticated_header = yes # TLS parameters # --------------------------------- # The default snakeoil certificate. Comment if using a purchased # SSL certificate. #smtpd_tls_cert_file=/etc/ssl/certs/ssl-cert-snakeoil.pem #smtpd_tls_key_file=/etc/ssl/private/ssl-cert-snakeoil.key # Uncomment if using a purchased SSL certificate. smtpd_tls_cert_file=/etc/ssl/certs/****.crt smtpd_tls_key_file=/etc/ssl/private/****.key # The snakeoil self-signed certificate has no need for a CA file. But # if you are using your own SSL certificate, then you probably have # a CA certificate bundle from your provider. The path to that goes # here. smtpd_tls_CAfile=/etc/ssl/certs/bundle_****.crt smtp_tls_note_starttls_offer = yes smtpd_tls_loglevel = 1 smtpd_tls_received_header = yes smtpd_tls_session_cache_timeout = 3600s tls_random_source = dev:/dev/urandom #smtpd_tls_session_cache_database = btree:${data_directory}/smtpd_scache #smtp_tls_session_cache_database = btree:${data_directory}/smtp_scache # Note that forcing use of TLS is going to cause breakage - most mail servers # don't offer it and so delivery will fail, both incoming and outgoing. This is # unfortunate given what various governmental agencies are up to these days. # # Enable (but don't force) all incoming smtp connections to use TLS. smtpd_tls_security_level = may # Enable (but don't force) all outgoing smtp connections to use TLS. smtp_tls_security_level = may # See /usr/share/doc/postfix/TLS_README.gz in the postfix-doc package for # information on enabling SSL in the smtp client. # SMTPD parameters # --------------------------------- # Uncomment the next line to generate "delayed mail" warnings #delay_warning_time = 4h # will it be a permanent error or temporary unknown_local_recipient_reject_code = 450 # how long to keep message on queue before return as failed. # some have 3 days, I have 16 days as I am backup server for some people # whom go on holiday with their server switched off. maximal_queue_lifetime = 7d # max and min time in seconds between retries if connection failed minimal_backoff_time = 1000s maximal_backoff_time = 8000s # how long to wait when servers connect before receiving rest of data smtp_helo_timeout = 60s # how many address can be used in one message. # effective stopper to mass spammers, accidental copy in whole address list # but may restrict intentional mail shots. smtpd_recipient_limit = 16 # how many error before back off. smtpd_soft_error_limit = 3 # how many max errors before blocking it. smtpd_hard_error_limit = 12 # This next set are important for determining who can send mail and relay mail # to other servers. It is very important to get this right - accidentally producing # an open relay that allows unauthenticated sending of mail is a Very Bad Thing. # # You are encouraged to read up on what exactly each of these options accomplish. # Requirements for the HELO statement smtpd_helo_restrictions = permit_mynetworks, warn_if_reject reject_non_fqdn_hostname, reject_invalid_hostname, permit # Requirements for the sender details smtpd_sender_restrictions = permit_sasl_authenticated, permit_mynetworks, warn_if_reject reject_non_fqdn_sender, reject_unknown_sender_domain, reject_unauth_pipelining, permit # Requirements for the connecting server smtpd_client_restrictions = reject_rbl_client sbl.spamhaus.org, reject_rbl_client blackholes.easynet.nl # Requirement for the recipient address. Note that the entry for # "check_policy_service inet:127.0.0.1:10023" enables Postgrey. smtpd_recipient_restrictions = reject_unauth_pipelining, permit_mynetworks, permit_sasl_authenticated, reject_non_fqdn_recipient, reject_unknown_recipient_domain, reject_unauth_destination, check_policy_service inet:127.0.0.1:10023, permit smtpd_data_restrictions = reject_unauth_pipelining # This is a new option as of Postfix 2.10, and is required in addition to # smtpd_recipient_restrictions for things to work properly in this setup. smtpd_relay_restrictions = reject_unauth_pipelining, permit_mynetworks, permit_sasl_authenticated, reject_non_fqdn_recipient, reject_unknown_recipient_domain, reject_unauth_destination, check_policy_service inet:127.0.0.1:10023, permit # require proper helo at connections smtpd_helo_required = yes # waste spammers time before rejecting them smtpd_delay_reject = yes disable_vrfy_command = yes # General host and delivery info # ---------------------------------- myhostname = mail.**** # mydomain = **** myorigin = /etc/hostname # Some people see issues when setting mydestination explicitly to the server # subdomain, while leaving it empty generally doesn't hurt. So it is left empty here. # mydestination = mail.example.com, localhost mydestination = # If you have a separate web server that sends outgoing mail through this # mailserver, you may want to add its IP address to the space-delimited list in # mynetworks, e.g. as 10.10.10.10/32. mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128 mailbox_size_limit = 0 recipient_delimiter = + inet_interfaces = all mynetworks_style = host # This specifies where the virtual mailbox folders will be located. virtual_mailbox_base = /var/vmail # This is for the mailbox location for each user. The domainaliases # map allows us to make use of Postfix Admin's domain alias feature. virtual_mailbox_maps = mysql:/etc/postfix/mysql_virtual_mailbox_maps.cf, mysql:/etc/postfix/mysql_virtual_mailbox_domainaliases_maps.cf # and their user id virtual_uid_maps = static:5000 # and group id virtual_gid_maps = static:5000 # This is for aliases. The domainaliases map allows us to make # use of Postfix Admin's domain alias feature. virtual_alias_maps = mysql:/etc/postfix/mysql_virtual_alias_maps.cf, mysql:/etc/postfix/mysql_virtual_alias_domainaliases_maps.cf # This is for domain lookups. virtual_mailbox_domains = mysql:/etc/postfix/mysql_virtual_domains_maps.cf # Integration with other packages # --------------------------------------- # Tell postfix to hand off mail to the definition for dovecot in master.cf virtual_transport = dovecot dovecot_destination_recipient_limit = 1 # Use amavis for virus and spam scanning content_filter = amavis:[127.0.0.1]:10024 # Header manipulation # -------------------------------------- # Getting rid of unwanted headers. See: https://posluns.com/guides/header-removal/ header_checks = regexp:/etc/postfix/header_checks # getting rid of x-original-to enable_original_recipient = noDovecot
## Dovecot configuration file # If you're in a hurry, see http://wiki2.dovecot.org/QuickConfiguration # "doveconf -n" command gives a clean output of the changed settings. Use it # instead of copy&pasting files when posting to the Dovecot mailing list. # '#' character and everything after it is treated as comments. Extra spaces # and tabs are ignored. If you want to use either of these explicitly, put the # value inside quotes, eg.: key = "# char and trailing whitespace " # Most (but not all) settings can be overridden by different protocols and/or # source/destination IPs by placing the settings inside sections, for example: # protocol imap { }, local 127.0.0.1 { }, remote 10.0.0.0/8 { } # Default values are shown for each setting, it's not required to uncomment # those. These are exceptions to this though: No sections (e.g. namespace {}) # or plugin settings are added by default, they're listed only as examples. # Paths are also just examples with the real defaults being based on configure # options. The paths listed here are for configure --prefix=/usr # --sysconfdir=/etc --localstatedir=/var # Enable installed protocols !include_try /usr/share/dovecot/protocols.d/*.protocol # A comma separated list of IPs or hosts where to listen in for connections. # "*" listens in all IPv4 interfaces, "::" listens in all IPv6 interfaces. # If you want to specify non-default ports or anything more complex, # edit conf.d/master.conf. #listen = *, :: # Base directory where to store runtime data. #base_dir = /var/run/dovecot/ # Name of this instance. In multi-instance setup doveadm and other commands # can use -i <instance_name> to select which instance is used (an alternative # to -c <config_path>). The instance name is also added to Dovecot processes # in ps output. #instance_name = dovecot # Greeting message for clients. #login_greeting = Dovecot ready. # Space separated list of trusted network ranges. Connections from these # IPs are allowed to override their IP addresses and ports (for logging and # for authentication checks). disable_plaintext_auth is also ignored for # these networks. Typically you'd specify your IMAP proxy servers here. #login_trusted_networks = # Space separated list of login access check sockets (e.g. tcpwrap) #login_access_sockets = # With proxy_maybe=yes if proxy destination matches any of these IPs, don't do # proxying. This isn't necessary normally, but may be useful if the destination # IP is e.g. a load balancer's IP. #auth_proxy_self = # Show more verbose process titles (in ps). Currently shows user name and # IP address. Useful for seeing who are actually using the IMAP processes # (eg. shared mailboxes or if same uid is used for multiple accounts). #verbose_proctitle = no # Should all processes be killed when Dovecot master process shuts down. # Setting this to "no" means that Dovecot can be upgraded without # forcing existing client connections to close (although that could also be # a problem if the upgrade is e.g. because of a security fix). #shutdown_clients = yes # If non-zero, run mail commands via this many connections to doveadm server, # instead of running them directly in the same process. #doveadm_worker_count = 0 # UNIX socket or host:port used for connecting to doveadm server #doveadm_socket_path = doveadm-server # Space separated list of environment variables that are preserved on Dovecot # startup and passed down to all of its child processes. You can also give # key=value pairs to always set specific settings. #import_environment = TZ ## ## Dictionary server settings ## # Dictionary can be used to store key=value lists. This is used by several # plugins. The dictionary can be accessed either directly or though a # dictionary server. The following dict block maps dictionary names to URIs # when the server is used. These can then be referenced using URIs in format # "proxy::<name>". dict { #quota = mysql:/etc/dovecot/dovecot-dict-sql.conf.ext #expire = sqlite:/etc/dovecot/dovecot-dict-sql.conf.ext } # Most of the actual configuration gets included below. The filenames are # first sorted by their ASCII value and parsed in that order. The 00-prefixes # in filenames are intended to make it easier to understand the ordering. !include conf.d/*.conf # A config file can also tried to be included without giving an error if # it's not found: !include_try local.confpasswd
root:x:0:0:root:/root:/bin/bash daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin bin:x:2:2:bin:/bin:/usr/sbin/nologin sys:x:3:3:sys:/dev:/usr/sbin/nologin sync:x:4:65534:sync:/bin:/bin/sync games:x:5:60:games:/usr/games:/usr/sbin/nologin man:x:6:12:man:/var/cache/man:/usr/sbin/nologin lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin mail:x:8:8:mail:/var/vmail:/usr/sbin/nologin news:x:9:9:news:/var/spool/news:/usr/sbin/nologin uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin proxy:x:13:13:proxy:/bin:/usr/sbin/nologin www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin backup:x:34:34:backup:/var/backups:/usr/sbin/nologin list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin libuuid:x:100:101::/var/lib/libuuid: syslog:x:101:104::/home/syslog:/bin/false mysql:x:102:106:MySQL Server,,,:/nonexistent:/bin/false messagebus:x:103:107::/var/run/dbus:/bin/false postfix:x:104:111::/var/spool/postfix:/bin/false dovecot:x:105:113:Dovecot mail server,,,:/usr/lib/dovecot:/bin/false dovenull:x:106:114:Dovecot login user,,,:/nonexistent:/bin/false landscape:x:107:115::/var/lib/landscape:/bin/false sshd:x:108:65534::/var/run/sshd:/usr/sbin/nologin myuser:x:1000:1000:MYUSER,,,:/home/myuser:/bin/bash vmail:x:5000:8::/var/vmail: clamav:x:109:118::/var/lib/clamav:/bin/false postgrey:x:110:119::/var/lib/postgrey:/bin/false amavis:x:111:120:AMaViS system user,,,:/var/lib/amavis:/bin/sh debian-spamd:x:112:121::/var/lib/spamassassin:/bin/shgroup
root:x:0: daemon:x:1: bin:x:2: sys:x:3: adm:x:4:syslog tty:x:5: disk:x:6: lp:x:7: mail:x:8: news:x:9: uucp:x:10: man:x:12: proxy:x:13: kmem:x:15: dialout:x:20: fax:x:21: voice:x:22: cdrom:x:24:user floppy:x:25: tape:x:26: sudo:x:27:user audio:x:29: dip:x:30:user www-data:x:33: backup:x:34: operator:x:37: list:x:38: irc:x:39: src:x:40: gnats:x:41: shadow:x:42: utmp:x:43: video:x:44: sasl:x:45: plugdev:x:46:user staff:x:50: games:x:60: users:x:100: nogroup:x:65534: libuuid:x:101: netdev:x:102: crontab:x:103: syslog:x:104: fuse:x:105: mysql:x:106: messagebus:x:107: mlocate:x:108: ssh:x:109: ssl-cert:x:110: postfix:x:111: postdrop:x:112: dovecot:x:113:mail,vmail dovenull:x:114: landscape:x:115: web:x:1000:www-data lpadmin:x:116: sambashare:x:117: clamav:x:118:amavis postgrey:x:119: amavis:x:120:clamav debian-spamd:x:121: vmail:x:5000: -
zensys over 9 yearsI just did and also chmod a-rx /etc/dovecot but than the error comes back.
-
 Michael Hampton over 9 yearsOf course, if you undo the fix then the problem will come back!
Michael Hampton over 9 yearsOf course, if you undo the fix then the problem will come back! -
zensys over 9 yearsBut my question was if there was a better fix. The error log suggest I should add a user to the dovecot group. But which one?