Why can I ping 10.0.0.0/8 addresses from a 192.168.1.0/24 subnet?
Solution 1
I thought 10.0.0.0/8 were all reserved addresses and that any sort of traffic going to those addresses was dropped.
No. It's true that it's a special range, but it's reserved for exactly the same purpose as 192.168.0.0/16 – it is a private address block for LAN usage. (There is also a third block, 172.16.0.0/12. See the IANA registry.)
All three private blocks act as normal unicast addresses and are routable locally, including between each other – they're just not routable across the global Internet. (What's actually dropped is traffic and route announcements between ISPs.)
So most likely you're pinging some host in your ISP's network, where they've decided to use 10.0.0.0/8. It could be a device on their internal network, or a 'management' VLAN on your router itself, or anything.
Solution 2
These are three most likely possibilities:
Your ISP assigns its clients the
10.0.0.0/8addresses. Your home router isn't advanced enough (nor needs to be) to limit routing private blocks upwards.You have an additional routing device between your router and ISP, like a cable modem, which communicates with your router over
10.0.0.0/8.You host or access
10.0.0.0/8network directly at your computer (i.e., a virtual machine network or some VPN).
The most important question is: why do you ping 10.10.10.140 specifically? Also, trying to access popular management services (HTTP, HTTPS, SSH, and Telnet) might reveal device identity and purpose.
Solution 3
You potentially could have a device on the network using that IP address that you are not aware of. The 10/8 range is not routable over the internet. I would take a look at your routes and see where its going.
Related videos on Youtube
Ryan Oliver Lanham
Updated on September 18, 2022Comments
-
Ryan Oliver Lanham over 1 year
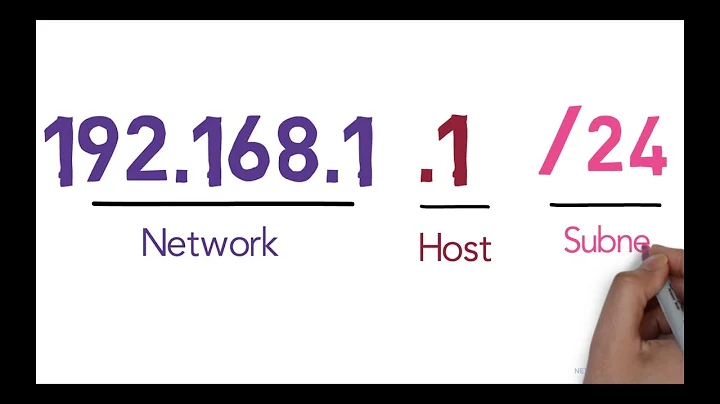
My home network uses a
192.168.1.0/24subnet, and when Iping 192.168.1.137I get a response saying the host is unavailable (as expected because I don't have any machines using that address)However, when I
ping 10.10.10.140it:- gets a response, and
- goes on forever.
I thought
10.0.0.0/8were all reserved addresses and that any sort of traffic going to those addresses was dropped. What am I pinging when I ping10.10.10.140? Is it IANA servers? -
Gordon Davisson over 4 yearsRunning
traceroute(tracerton Windows) to 10.10.10.140 might fill in some of the details. -
Kevin over 4 yearsIt could even be another consumer's address (behind the same CGN)! They really should be firewalling that, but a lot of ISPs are amazingly incompetent.
-
user1686 over 4 years@Kevin Uhh, why should they firewall one customer from another just because they're both behind CGNAT now? If you can talk to other ISPs' customers, you should be able to talk to the same ISP's customers.
-
Stobor over 4 yearsIt's not routable over the internet, but it is routable over any private network which acknowledges its existence. It is possible that Ryan's ISP is using such a private network (CGNAT - Carrier Grade NAT), and that Ryan's router's external IP is the carrier's private 10/8 network.
-
rmunn over 4 years@grawity - When you talk to other ISPs' customers, it goes through a firewall so that if you're trying Evil Stuff™ with your IP packets, the firewall should block those packets. (The definition of Evil Stuff™ is, of course, situation-dependent). When you're talking to other customers of your ISP, you shouldn't get more access privileges: those conversations should go through a firewall as well. What Kevin seems to be implying is that many ISPs don't put a firewall between two customers behind the same CGN, so any Evil Stuff™ you might try on those connections would work.
-
user1686 over 4 years@rmunn: That's fine, but it shouldn't classify regular pings and TCP connections as Evil Stuff™. Even when customers get placed behind a CGNAT, they still have their own firewalls at home to block/allow regular inbound connections – the ISP should have no need to blanket forbid those.
-
 dgnuff over 4 yearsT-Mobile does exactly this. I have a laptop here connected using tethering on my T-Mobile phone. Tracert to 8.8.8.8 shows my phone's lan connection in the 192.168.0.0/16 block, but the next 8 hops above that are all in various /16's in the 10.0.0.0/8 block.
dgnuff over 4 yearsT-Mobile does exactly this. I have a laptop here connected using tethering on my T-Mobile phone. Tracert to 8.8.8.8 shows my phone's lan connection in the 192.168.0.0/16 block, but the next 8 hops above that are all in various /16's in the 10.0.0.0/8 block. -
David Schwartz over 4 years@rmunn The purpose of those firewalls is often not to protect their customers but to prevent them from having inconvenient coordination problems with other ISPs. In that case, it makes a lot of sense to filter traffic between your own customers more lightly than traffic you exchange with other ISPs. Also, it's often hard to filter all your customers from each other because they're all over the place. You meet peers at fewer points so it's easier to firewall there.
-
ayao1337 over 4 yearsYeah that's accurate. I didn't consider that originally so I edited my answer to match.
-
duct_tape_coder over 4 yearsYou know it's interesting: I'm pretty sure when I went through the Network+ training back in 2009, it was 192.168.0.0/24, 172.16.0.0/16, and 10.0.0.0/8 for the Class C, B, and A networks. Did they expand it, or am I just remembering wrong?
-
Weckar E. over 4 yearsEven then, a connection between any two consumers should function identically, regardless of whether they share an ISP or not.
-
user1686 over 4 years@duct_tape: No, the total ranges were always the same. But in classful routing era, 192.168.0.0/16 was originally called "a block of 256 class-C networks", and each one of those networks was a /24 due to being class-C. (Same goes for 172.16.0.0/12 being a block of 16 consecutive class-B networks.) However, this system had already been some ten years obsolete when you took your training – and is even more obsolete now. So the range is still the same, but instead of calling it "256 consecutive /24s" it is now simply a /16 network, subnettable at any level.
-
Gordon Davisson over 4 years@duct_tape_coder See my answer at networkengineering.se for more about the history of the private network ranges.