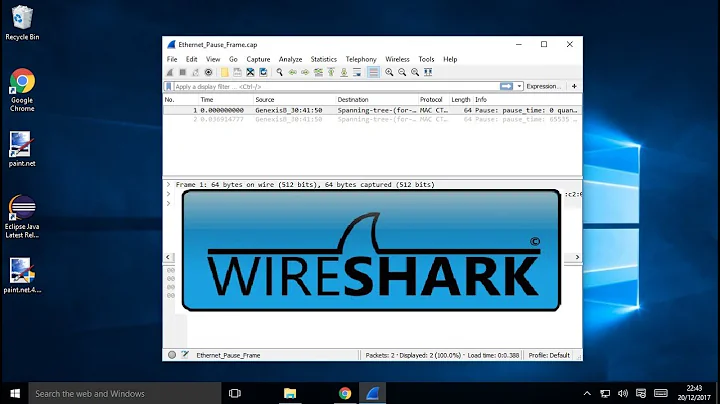
Wireshark and Windows Firewall
Solution 1
Where is Wireshark running, on the destination machine or on the source machine? If it's running on the source machine I would expect to see behavior as in # 2. You should see the outgoing connection from the source machine in Wireshark but no return traffic. I'm curious, does the Windows Firewall send a RST when it blocks incoming connections or does it silently drop the connection?
Come to think of it, I might expect to see behavior as in # 2 on the destination machine as well due to the fact that the incoming connection has to be initiated before Windows firewall can do it's job. It can't block a connection that hasn't made it to the destination machine and up to layer 3 yet.
Solution 2
I would think so. The firewall is software within the O/S. The packet still has to come into the machine, bubble up through the networking stack until it hits the firewall, at which point it's accepted and passed or denied and blocked. I would expect this behavior.
Now if the firewall existed between the Internet and your machine, you would see nothing in Wireshark if that external firewall blocked the packet(s).
Related videos on Youtube
Franz Wong
Currently a Site Reliability Engineer at Take 2 Interactive. Formerly a Site Reliability Engineer for the Stack Exchange network. Prior to my work for Stack Exchange I worked for a small software developer in Sydney, Australia.
Updated on September 17, 2022Comments
-
Franz Wong over 1 year
If I block a port in the Windows Firewall, and then attempt a connection to that port from another PC, what should I expect to see in Wireshark?
When running wireshark at the destination machine ('server' for lack of a better term), should I see:
- No inbound or outbound connections (which is what I would expect with a hardware firewall)
- An inbound connection attempt, but no outbound
At the moment I'm seeing #2 - I can see the inbound connection attempt, but I never see any response from the machine.
Should this be the expected behaviour?
-
Franz Wong over 14 yearsI suspected as much. I've never really relied on the Windows firewall for anything before, I usually use a hardware firewall
-
Franz Wong over 14 yearsAlso, by the looks of it, it silently drops the connection, because there's absolutally no traffic going back to the source IP, not even a Refused notification.
-
 joeqwerty over 14 yearsThat makes sense based on my assumption in my second paragraph. Wireshark works from layer 2 and up, while I'm guessing that the Windows firewall works at layer 3 and up (which is probably why you can only create rules that operate at layers 3 and up and not at layer 2). So Wireshark sees the connection at layers 2 and 3 before the Windows firewall acts. Once the Windows firewall acts on the connection, it kills it (I don't know what method it uses) and so there's nothing coming back down the stack for Wireshark to see.
joeqwerty over 14 yearsThat makes sense based on my assumption in my second paragraph. Wireshark works from layer 2 and up, while I'm guessing that the Windows firewall works at layer 3 and up (which is probably why you can only create rules that operate at layers 3 and up and not at layer 2). So Wireshark sees the connection at layers 2 and 3 before the Windows firewall acts. Once the Windows firewall acts on the connection, it kills it (I don't know what method it uses) and so there's nothing coming back down the stack for Wireshark to see. -
 joeqwerty over 14 years@Farseeker: Thanks for accepting my answer. It's nice to have someone who's technical savvy I admire give me a thumbs up.
joeqwerty over 14 years@Farseeker: Thanks for accepting my answer. It's nice to have someone who's technical savvy I admire give me a thumbs up. -
Franz Wong over 14 yearsAdmire? Well there's a word I don't think I've heard in my direction before. Anyhoo your ServerFault rep is looking quite healthy :) I was surprised to see you on here to be honest, I was expecting a different batch of users!
-
 joeqwerty over 14 yearsYeah, I don't get here very often. Yesterday was a fluke I guess. ;)
joeqwerty over 14 yearsYeah, I don't get here very often. Yesterday was a fluke I guess. ;)