Cisco asa 5505 to use internal DNS server
You're going about this correctly. I guess the reasoning for this error is that if your DNS server is dynamically configured there's a chance it could lose that IP address and break DNS for the rest of your clients. I would put a static IP on the DNS server and just change the DHCP range to exclude 10.5.1.2.
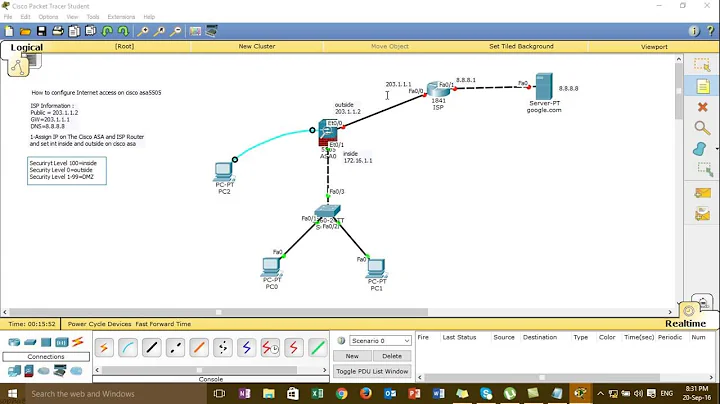
Related videos on Youtube
rzetterberg
An evolutionary algorithm in form of a human being.
Updated on September 18, 2022Comments
-
 rzetterberg over 1 year
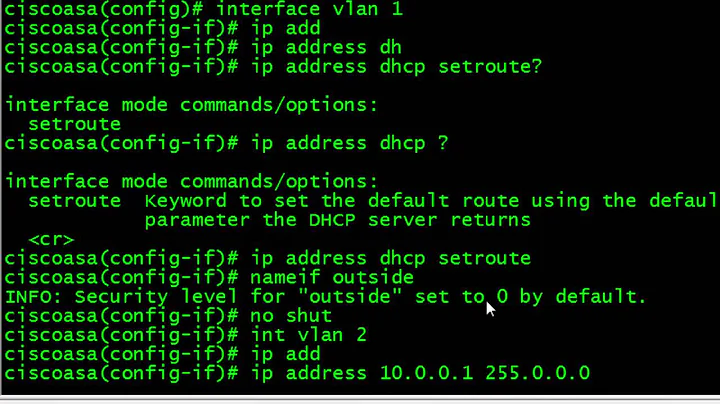
rzetterberg over 1 yearI have just installed and configured a ASA 5505 firewall (basic license) which has 3 VLANs (outside, trusted, untrusted) and the configuration is really basic.
Outside is for internet, trusted is for LAN computers, untrusted is for Wifi.
We have an internal server connected to trusted with a static ip of 10.5.1.2. That server runs a Bind DNS instance. The server also runs 2 VPS instances. To make it easy to access the VPS instances they are given a domain name and the DNS instance is used to supply computers of the network with the ip for those VPS instances.
I tried to add the internal server as the primary DNS server and Googles public slave DNS (8.8.4.4) as secondary:
mastermind(config)# dhcpd dns 10.5.1.2 8.8.4.4 address overlap with dhcp pool ip addressesHowever that did not work. Do I need to reserve that ip so that it's not in the DHCP pool? Or am I going at this totally wrong altogether?
Relevant config settings:
ASA Version 8.4(1) ! interface Vlan1 nameif outside security-level 0 ip address dhcp ! interface Vlan2 nameif trusted security-level 100 ip address 10.5.1.1 255.255.255.0 ! interface Vlan3 no forward interface Vlan2 nameif untrusted security-level 50 ip address 10.4.1.1 255.255.255.0 ! interface Ethernet0/0 ! interface Ethernet0/1 switchport access vlan 2 # Ethernet0/2 to Ethernet0/6 has identical configuration ! interface Ethernet0/7 switchport access vlan 3 ! dns server-group DefaultDNS domain-name mastermind.local object network obj_any subnet 0.0.0.0 0.0.0.0 ! object network obj_any nat (trusted,outside) dynamic interface route outside 0.0.0.0 0.0.0.0 10.15.166.1 1 aaa authentication ssh console LOCAL ssh 0.0.0.0 0.0.0.0 trusted dhcpd dns 8.8.8.8 8.8.4.4 dhcpd auto_config outside ! dhcpd address 10.5.1.2-10.5.1.32 trusted dhcpd enable trusted ! dhcpd address 10.4.1.2-10.4.1.32 untrusted dhcpd enable untrusted ! -
 rzetterberg about 12 yearsPerfect. I just changed the pool to exclude the 10.5.1.2 ip, and since the server isn't using DHCP it worked. Thank you! :)
rzetterberg about 12 yearsPerfect. I just changed the pool to exclude the 10.5.1.2 ip, and since the server isn't using DHCP it worked. Thank you! :)