Opened some ports with iptables but they aren't open
Solution 1
Are you sure your applications are actually listening on those ports (or are even running)? A port won't show as open in an nmap scan or to telnet if there's nothing listening on it. I'd guess that you haven't started your mail server yet, or it's not configured to listen on those ports. You can use netstat to see what services are listening on what ports on your system.
Solution 2
Your netstat output shows that you don't have an SMTP server listening on ports 465 and 587. Reconfigure the SMTP server and try again.
The same applies to your web server and port 443.
Related videos on Youtube
mouseowl
Updated on September 18, 2022Comments
-
mouseowl over 1 year
I'm running a Debian 7 server via Linode VPS, and have recently installed/configured a mail server using Postfix and Dovecot. The final step to complete this was to open up ports 993, 995, 465, and 587. I did this by correctly adding rules allowing those ports in iptables.
However when I tested to see if they were open using telnet and then nmap, port 465 and 587 were not open. I also noticed from the nmap scan that the https port 443 was also not open when it should be according to my rules.
I also have an Ubuntu server on linode with the same mail setup and same firewall rules, and it works fine (except for the https port).
What is going on? I can't figure out why this is happening.
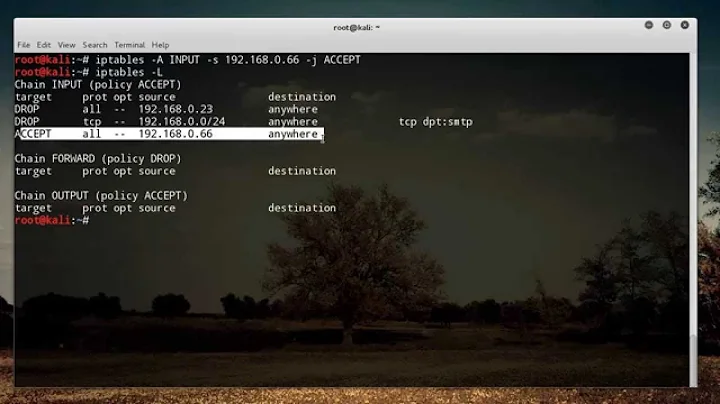
Here are my iptables rules:
*filter # Allow all loopback (lo0) traffic and drop all traffic to 127/8 that doesn't use lo0 -A INPUT -i lo -j ACCEPT -A INPUT -d 127.0.0.0/8 -j REJECT # Accept all established inbound connections -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT # Allow all outbound traffic - you can modify this to only allow certain traffic -A OUTPUT -j ACCEPT # Allows SMTP access #-A INPUT -p tcp --dport 25 -j ACCEPT -A INPUT -p tcp --dport 465 -j ACCEPT -A INPUT -p tcp --dport 587 -j ACCEPT # Allows pop and pops connections #-A INPUT -p tcp --dport 110 -j ACCEPT -A INPUT -p tcp --dport 995 -j ACCEPT # Allows imap and imaps connections #-A INPUT -p tcp --dport 143 -j ACCEPT -A INPUT -p tcp --dport 993 -j ACCEPT # Allow HTTP and HTTPS connections from anywhere (the normal ports for websites and SSL). -A INPUT -p tcp --dport 80 -j ACCEPT -A INPUT -p tcp --dport 443 -j ACCEPT # Allow SSH connections # # The -dport number should be the same port number you set in sshd_config # -A INPUT -p tcp -m state --state NEW --dport 22 -j ACCEPT # Allow ping -A INPUT -p icmp -j ACCEPT # Log iptables denied calls -A INPUT -m limit --limit 5/min -j LOG --log-prefix "iptables denied: " --log-level 7 # Drop all other inbound - default deny unless explicitly allowed policy -A INPUT -j DROP -A FORWARD -j DROP COMMITHere is the output of
iptables -L:Chain INPUT (policy ACCEPT) target prot opt source destination fail2ban-ssh tcp -- anywhere anywhere multiport dports ssh ACCEPT all -- anywhere anywhere REJECT all -- anywhere loopback/8 reject-with icmp-port-unreachable ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED ACCEPT tcp -- anywhere anywhere tcp dpt:ssmtp ACCEPT tcp -- anywhere anywhere tcp dpt:submission ACCEPT tcp -- anywhere anywhere tcp dpt:pop3s ACCEPT tcp -- anywhere anywhere tcp dpt:imaps ACCEPT tcp -- anywhere anywhere tcp dpt:http ACCEPT tcp -- anywhere anywhere tcp dpt:https ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh ACCEPT icmp -- anywhere anywhere LOG all -- anywhere anywhere limit: avg 5/min burst 5 LOG level debug prefix "iptables denied: " DROP all -- anywhere anywhere Chain FORWARD (policy ACCEPT) target prot opt source destination DROP all -- anywhere anywhere Chain OUTPUT (policy ACCEPT) target prot opt source destination ACCEPT all -- anywhere anywhere Chain fail2ban-ssh (1 references) target prot opt source destination RETURN all -- anywhere anywhereHere is my nmap portscan:
Starting Nmap 6.40 ( http://nmap.org ) at 2014-01-04 21:09 EST Nmap scan report for ******.com (***.**.***.**) Host is up (0.11s latency). Not shown: 93 filtered ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http 443/tcp closed https 465/tcp closed smtps 587/tcp closed submission 993/tcp open imaps 995/tcp open pop3s Nmap done: 1 IP address (1 host up) scanned in 2.64 secondsAny help would be appreciated. Thanks!
Active Internet connections (only servers) Proto Recv-Q Send-Q Local Address Foreign Address State User Inode tcp 0 0 *:imaps *:* LISTEN root 5002 tcp 0 0 *:pop3s *:* LISTEN root 4983 tcp 0 0 localhost:mysql *:* LISTEN mysql 4947 tcp 0 0 *:ssh *:* LISTEN root 3648 tcp 0 0 *:smtp *:* LISTEN root 5531 tcp6 0 0 [::]:imaps [::]:* LISTEN root 5003 tcp6 0 0 [::]:pop3s [::]:* LISTEN root 4984 tcp6 0 0 [::]:http [::]:* LISTEN root 7548 tcp6 0 0 [::]:ssh [::]:* LISTEN root 3650 tcp6 0 0 [::]:smtp [::]:* LISTEN root 5533 -
mouseowl over 10 yearsThanks. I've edited my post with netstat listening services.
-
 MDMarra over 10 yearsNetstat's -n option will show port numbers, if you do that, you'll see that the you have nothing listening on the ports that you're complaining are closed.
MDMarra over 10 yearsNetstat's -n option will show port numbers, if you do that, you'll see that the you have nothing listening on the ports that you're complaining are closed. -
mouseowl over 10 yearsI double checked my configuration of Postfix, and it's exactly the same as the one on my functioning mailserver. I can't figure out what's wrong. The only thing I can think of is that it could have something to do with the difference between Ubuntu and Debian



![IPTABLES [PART-2] : COMMAND SYNTAX WITH LIVE DEMO!](https://i.ytimg.com/vi/H1WPwAjMXRo/hq720.jpg?sqp=-oaymwEcCNAFEJQDSFXyq4qpAw4IARUAAIhCGAFwAcABBg==&rs=AOn4CLC_dR6RBTuw8sdjmY1pdWf1ZcA-wQ)